Threat Hunting is FINALLY a hot topic, and in the past couple of months the security community has been sharing amazing resources on how to hunt with the help of open source tools. One in particular that has got a lot of attention for endpoint visibility has been Sysmon, and with its latest capabilities added in version 6, hunting even for named pipe pivoting has become easier.
A few projects that I have read recently are awesome, and I highly recommend to take a look at them:
Some of the things that I love about most the projects out there are the different ways how sysmon configs are being put together and how data is being consolidated and presented for hunting campaigns. Therefore, in this post, I will show you how you can also create your own Sysmon dashboard but with the help of an ELK stack. This will help you to tune your initial Sysmon configurations and get a good overview of what you can see and hunt for in your lab. If you haven't yet read my previous series "Setting up a Pentesting... I mean, a Threat Hunting Lab", I recommend you to do it before continuing reading (At least, for the purpose of this post, read and follow the steps in Part 5 & Part 6 in order to be ready to build your dashboard).
Current Kibana view
 |
| Figure 1. Kibana default discover view. |
Building a Sysmon Dashboard
Creating Visualizations
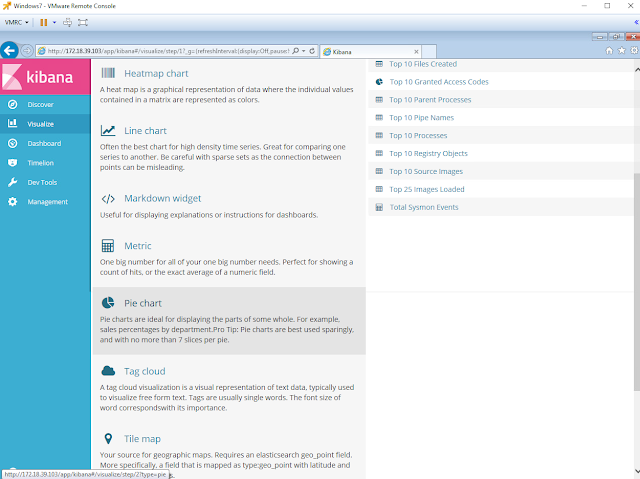
To get started click on the option "visualize" on the left panel. Next, you will have two options to choose from:
- Create New Visualization - Showing different types that you can use to present your data
- Open a Saved Visualization
Since this is our first visualization, then we will have to select the specific type we want to create. Make sure you review the Kibana User Guide - Creating a Visualization during this section to have a better understanding of each visualization type.
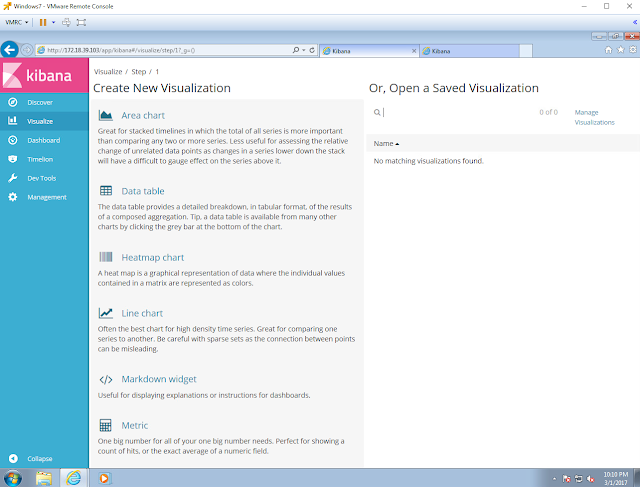 |
| Figure 2. Visualize options. |
I like to use Data Tables because they are really flexible to show long strings of data and large number of events in a small graph. Data Tables display the raw data of a composed aggregation. Click on Data Table to create one.
 |
| Figure 3. Creating a Data Table. |
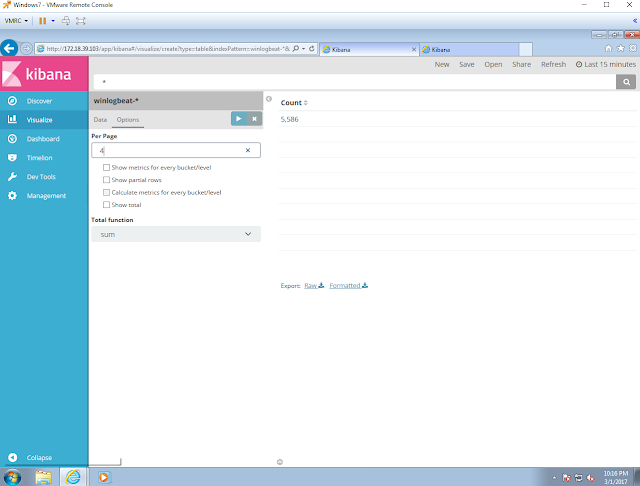
We are creating all of our visualizations from scratch so select the index that you want to use for it. In my case, I selected my only index, winlogbeat-*.
 |
| Figure 4. Creating a Data Table. |
Next, you will get a plain visualization template which you will use to create your own one. One main thing that we need to do is select the data field that we want to use for this table, but first we will have to select a bucket type. The rows of the data table are called buckets. You can define buckets to split the table into rows or to split the table into additional tables [Source]. Select the Split Rows bucket type.
 |
| Figure 5. Creating a Data Table. |
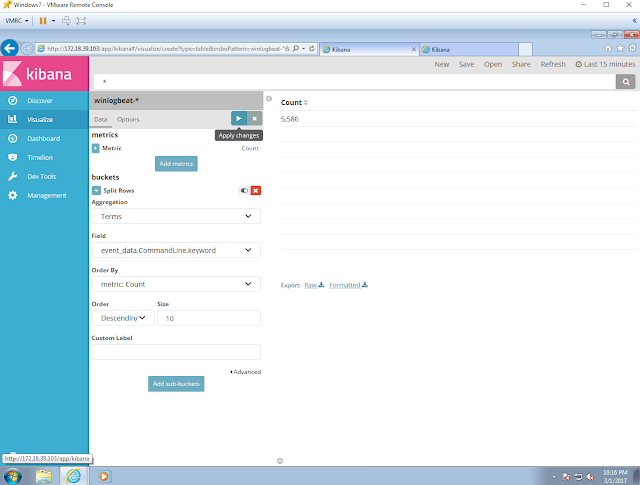
Buckets support aggregations. Select the aggregations type "Terms". A terms aggregation enables you to specify the top or bottom n elements of a given field to display, ordered by count of a custom metric [Source]
 |
| Figure 6. Creating a Data Table. |
Next, select the field that you want to use for the visualization. For this first exercise, I chose the CommandLine field as shown in figure 8. One important thing to mention is that I use Keyword data fields (Keyword Analyzers) because it returns the entire string as a single token [Source]. For example, I chose event_data.CommandLine.keyword.
 |
| Figure 7. Creating a Data Table. |
 |
| Figure 8. Creating a Data Table. |
Then set the number of values that you want to show. The data by default will be ordered "Descending". You can set the size to 25 and it will show you the Top 25 values. Lets set it to 10 for this exercise.
 |
| Figure 9. Creating a Data Table. |
 |
| Figure 10. Creating a Data Table. |
Next, you can also adjust the number of values you want to show per page. This will depend on how much space you want to use with your data table. I always set it to 4 to fit several data tables in one dashboard.
 |
| Figure 11. Creating a Data Table. |
 |
| Figure 12. Creating Data Table. |
Apply the changes to your visualization by clicking on the blue triangle to the right of "options" as shown in figure 13 below.
 |
| Figure 13. Creating a Data Table. |
Now you will see events showing on the right side of your visualization console. Four values per page and two pages in the last 15 minutes.
 |
| Figure 14. Creating a Data Table. |
Save your visualization by clicking on the option Save. Give it a name and click Save. You will get a dark green confirmation message as shown in figure 18 below.
 |
| Figure 15. Saving Data Table. |
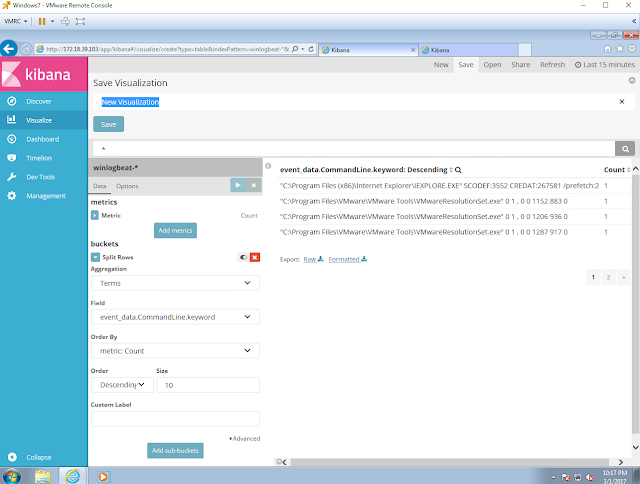 |
| Figure 16. Saving Data Table. |
 |
| Figure 17. Saving Data Table. |
 |
| Figure 18. Saving Data Table. |
Creating a new Dashboard
Click Dashboard in the side navigation. If you haven’t previously viewed a dashboard, Kibana displays an empty dashboard [Source]. Click Add in the menu bar to add your saved visualization to it.
 |
| Figure 19. Creating a Dashboard |
As you can see, our Top 10 Command Line is the only one available. Click on it and it will get added to your Dashboard.
 |
| Figure 20. Creating a Dashboard. |
 |
| Figure 21. Adding visualization to dashboard. |
Next, you can start saving your dashboard with your first visualization by clicking on "Save". Give your dashboard a name and if you want to save it to open always with a specific time range, set the desired time range and click on the "Store time with dashboard" checkbox as shown in figure 26 below.
 |
| Figure 22. Saving new dashboard. |
 |
| Figure 23. Saving new dashboard. |
 |
| Figure 24. Saving a new dashboard. |
 |
| Figure 25. Adjusting Time Range for new Dashboard. |
 |
| Figure 26. Saving dashboard with option "Store time with dashboard". |
 |
| Figure 27. Saving new dashboard. |
Creating a new visualization for our new dashboard
Let's create a different visualization. Lets select a Pie Chart.
 |
| Figure 28. Creating a Pie Chart. |
- Select the data field that you want to use in the visualization
- Set the number of values to show in the data table
- Apply Changes
 |
| Figure 29. Creating a Pie Chart. |
As you can see, in figure 29 above, there is an event id (4656) that does not belong to the Sysmon ones. This is because I am also sending Windows event logs to my ELK stack. An easy fix is just to use the search bar and run a query to show only source_name:"Microsoft-Windows-Sysmon". That will make your visualization to work only with the results of your query which will be only Sysmon logs.
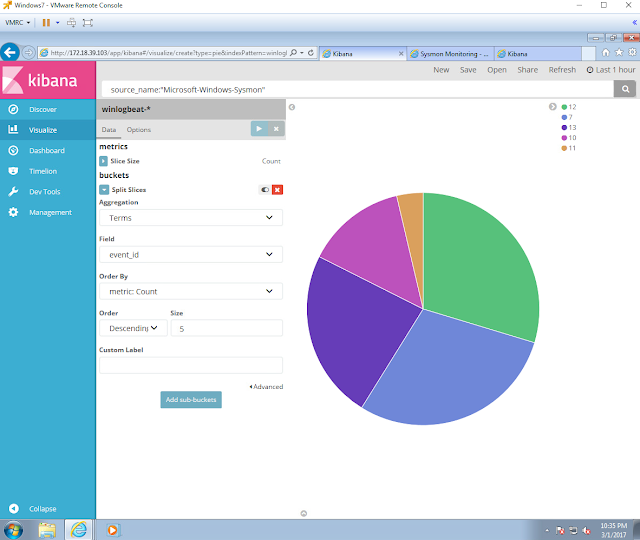 |
| Figure 30. Creating a Pie Chart. |
Next, you can use the options button to change the shape of your graph. I always like to set it to the Donut style. Then, you can save your visualization and add it to your new dashboard the same way how we did it before with our Data table.
 |
| Figure 31. Creating a Pie Chart. |
How can I exclude specific values in my visualization?
In figure 32 below, my top destination IP value is 172.18.39.103 and the problem with it is that the IP belongs to my own ELK server. Therefore, I need to filter that value out in my visualization. You have 2 options:
- Add exclusions in your Sysmon Config (Recommended - Best Practice)
- Create/Apply a filter to you visualization (good exercise for you)
 |
| Figure 32. Excluding values in visualization. |
For the purpose of this exercise:
- Click on the value you want to filter out, and it will actually set a filter to only show that value by default
- Hover over the filter that you just created below the search bar
- Select the (-) magnifier glass and you will see that the filter turns red which means that the value is now being filtered out
 |
| Figure 33. Excluding values in visualization. |
 |
| Figure 34. Excluding values in visualization. |
 |
| Figure 35. Excluding values in visualization. |
Creating all the needed visualization for our Sysmon Dashboard
Total Sysmon Events - Metric Visualization
By selecting winlogbeat-* index, the Metric Visualization will count all the events in our index. Make sure that if you want only Sysmon logs, you run a query for source_name:"Microsoft-Windows-Sysmon" as shown in figure 36 below.
 |
| Figure 36. Sysmon Metrics. |
Sysmon Event IDs - Pie Chart Visualization
 |
| Figure 37. Sysmon Event IDs. |
Registry Event Types - Pie Chart Visualization
 |
| Figure 38. Registry Event Types.. |
Top 10 Granted Access Codes - Pie Chart Visualization
 |
| Figure 39. Granted Access Codes. |
Top 10 Destinations - Pie Chart Visualization
 |
| Figure 40. Destination IPs. |
Top 10 Destination Ports - Pie Chart Visualization
 |
| Figure 41. Destination Ports. |
Top 10 Parent Processes - Data Table Visualization
 |
| Figure 42. Parent Processes. |
Top 10 Processes - Data Table Visualization
 |
| Figure 43. Processes. |
Top 10 Command Line - Data Table Visualization
 |
| Figure 44. Command Line. |
Top 10 Pipe names - Data Table Visualization
 |
| Figure 45. Pipe Names. |
Top 10 Source Images - Data Table Visualization
 |
| Figure 46. Source Images. |
Top 25 Images loaded - Data Table Visualization
 |
| Figure 47. Images Loaded. |
Top 10 Registry Objects - Data Table Visualization
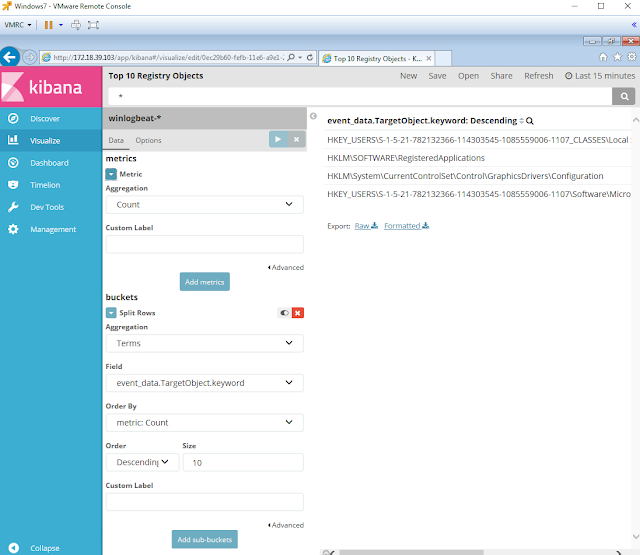 |
| Figure 48. Registry Objects. |
Top 10 Files Created - Data Table Visualization
 |
| Figure 49. Files Created. |
How do I delete visualizations?
- In the dashboard console click Add and select the option "Manage Visualizations"
- Click on the checkbox of the visualization as shown in figure 51
- Select the option "Delete"
- Confirm that you are deleting the visualization
 |
| Figure 50. Add visualizations console. |
 |
| Figure 51. Selecting the visualization. |
 |
| Figure 52. Deleting visualization - Confirmation. |
 |
| Figure 53. Visualizations. |
All the visualizations needed for our Sysmon Dashboard
 |
| Figure 54. Visualizations ready. |
Saved visualizations added to our Sysmon Dashboard
 |
| Figure 55. Sysmon Dashboard. |
How do I clean my dashboard or Index?
Stop your Winlogbeat services on your endpoints to stop them from sending logs to your ELK server.
 |
| Figure 56. Stopping Winlogbeat service. |
On your ELK server delete your index by using the following command:
curl -XDELETE 'localhost:9200/winlogbeat-*?pretty'
https://www.elastic.co/guide/en/elasticsearch/reference/current/indices-delete-index.html
 |
| Figure 57. Deleting Index. . |
Refresh your discover view and you dashboard. You will see that there are no records available.
 |
| Figure 58. Clean Index. |
 |
| Figure 59. Clean Dashboard. |
Start sending logs back to your ELK Stack
Start your winlogbeat service on your endpoints and refresh your Discover view and Dashboard.
 |
| Figure 60. Starting Winlogbeat service. |
 |
| Figure 61. Discover view. |
Final Sysmon Dashboard
 |
| Figure 57. Final Sysmon Dashboard. |
That's it! In my next posts I will be using the same approach to start creating targeted dashboard hunts for different TTPs.
Feedback is greatly appreciated! Thank you.

Your ELK series is fantastic and exactly what I was looking for!!
ReplyDeleteHey Marcus! Thank you for the feedback man. I am glad to hear that it is helpful. I will be adding some basic data science concepts/techniques to play with the data from Elasticsearch soon :)
DeleteGreat post Roberto! Thanks for creating this. Some feedback: I think these posts may be easier to follow if they were a collection of 1 or more short narrated videos instead.
ReplyDeleteThanks for the very interesting article. Will the amount events and data indexed be a problem?
ReplyDeleteThe article is quite appealing and attractive. We are the world's leading database supplier of email lists. We at Pegasi Media Group have with all types of companies of all the sizes and domains to provide you a wide choice with respect to the geographical location and the customer likes and dislikes.Our contact discovery services is very good at finding out the customer information which gives you the idea about what the customer wants.Data Building| B2B List Building Services
ReplyDeleteGreat tutorials! I wish you could add some new ones on how to add for e.g. Bro, Snort or something like that so we have also some NIDS in place.
ReplyDeleteDo you plan perhaps on a tutorial like that?
I have tried following some other ones, but could not configure Bro through Filebeat.. i cannot get data into ElasticSearch, although it recognizes Logstash index pattern, but when I try to query some Bro specific logs - there are no results.
A state of art, Thanks for sharing.
ReplyDeleteI am often to blogging and i really appreciate your content. The article has really peaks my interest. I am going to bookmark your site and keep checking for new information
ReplyDeleteQuickBooks offers several features, one of which is the QuickBooks Multi-User Mode. If you have switched from single-mode to multi-user mode then there is a possibility that multi-user mode may not work and you face the problem of QuickBooks Multi-user Mode Not Working. So than consider QuickBooks Customer Service and get immediate assistance.
I read a many blog post and this post is amazing and lot learn based topic. Thanks for sharing with us.
ReplyDeleteThe most popular brand of printer used by millions of users is the Brother printer. At this time, the user needs a quality job, quick connectivity, and user-friendly features of the brother printer. It helps to make your job easy and saves you time as well. The most popular problem that usually comes with the printer is the printer in error state issues. When using a brother printer, when your printer stops working and reveals that the printer is in an error state, this issue is called Brother Printer in Error State, which means that the problem is in your printer itself. Don't frustrate yourself. For further assistance, you can contact our Technical Experts for Printer Customer Service. They will provide accurate solutions to your issues at any time.
Some really wondrous work on behalf of the owner of this site, perfectly great subject material.
ReplyDeleteHow To Download AOL Desktop Gold
When you contact us, we respond quickly and will arrive on-site within 30 minutes or less. We get right to work, employing our proven Water Damage Restoration Service process so that you can get back to enjoying your home or running your business.
ReplyDeleteWhen Ketu is placed in different houses of planets, then plays a lot of different and significant roles. Ketu in 3rd house can give both positive and negative results for natives. But in most cases, it is not good as it ruins the relationship and can also lead to bad marriage or delay in marriage. Sometimes, due to this placement, people do evil deeds. If you want a permanent and rigid treatment of this placement, I suggest you to contact Dr. Vinay Bajrangi.
ReplyDeleteI read your post. I am really glad to read your post. Thanks for sharing with us.
ReplyDeleteGear Boxes Manufacturers
Gear Boxes Manufacturer
Gear Boxes Manufacturer in India
Gear Boxes in India
nice
ReplyDeletepitbull puppies for sale
pitbull puppies for sale
pitbulls for sale
Glock 17 for sale cheap online without License overnight delivery (glockgunstore.com)
glock 30 for sale
uzi pistol for sale
Browning Hi-Power 9mm
I read your post. I am really thankful for this information. Thanks for sharing with us.
ReplyDeleteAT&T Yahoo is a user-friendly mailing platform that is preferred by millions of users across the globe. Yahoo email inside AT&T has many features but sometimes, users may face ATT Email Login issues. To rectify the situation, you can contact professionals to fix the issues. You can reach us immediately for top solutions via the AT&T Yahoo email customer service number.
Welldone information. Thanks for sharing with us.
ReplyDeleteIf you want to get Free Spin And Coin on coin master then you can join us and spend your quality time playing the coin master game and get free spins and coins with a daily link.
I read your post. It is amazing and helpful information for me. Thanks for sharing with everyone. I am Sofi Vergara, I am working as a tech expert at Yahoo support. I have 3 years of experience in this field. If you have any problems related to yahoo help etc, then please contact me for instant help related to Yahoo email problems.
ReplyDeleteI read your post. It is amazing and helpful information for me. Are you looking for a solution How to Delete Cache App Activity? Cash App Activity is a record of all transaction activity from sending or receiving the money to your contacts. To delete your cache app activity, you have it in the right place. If you have any questions regarding deleting Cash App transaction history, please contact us at our Cash App customer service.
ReplyDeleteBusiness central Plan all your tasks, estimate the cost forecast and indicate the availability of your business resources. In addition, thanks to the integration of the Microsoft Dynamics 365 management modules, the production and resource saving plans will be generated automatically. dynamics 365 finance and operations
ReplyDeleteAre you planning your next flight travel trip with Allegiant Airlines? Speak to person at Allegiant Air representative. Clients can drop reservations online through the Manage Travel segment of www.allegiantair.com and can drop or make changes to reservations by reaching Allegiant's Reservations Center and talk to a person at allegiant air on this number (702) 505-8888toll-free.
ReplyDeleteWondering How to get a Refund from United Airlines? Know United Airlines refund policy, call the experts and process your refund requests.
ReplyDeleteOn the off chance that you ended up booking your trip with Delta Air Lines and need to drop, you're perfectly positioned! Here is all the data you want to explore its 2021 dropping approach and figure out what arrangements apply to your circumstance.
ReplyDeleteDelta Airlines Office Jeddah
Delta Airlines Office Jeddah
Are you planning your next flight travel trip with Allegiant Airlines? Speak to a person at Allegiant Air representative. Clients can drop reservations online through the Manage Travel segment of www.allegiantair.com and can drop or make changes to reservations by reaching Allegiant's Reservations Center and Allegiant Air representative on this number (702) 505-8888 toll-free.
ReplyDeleteVery informative and impressive post you have written, this is quite interesting and i have went through it completely, an upgraded information is shared, keep sharing such valuable information. Delta 8 buy online
ReplyDeletemobile learning services organizations add competencies in their overall learning architecture to increase proficiency and performance in the office.
ReplyDeleteDynamics 365 Customer Insights enables the business to build customer segments with simple and powerful tools that facilitate segmentation by any data ingested, KPIs, metrics generated or values obtained from Machine Learning engines .
ReplyDeleteYou will only need to pay the monthly cost of the licenses for each of your employees who access the system, exactly as is already being done with the Office-365 model. NAV to Business Central Upgrade
ReplyDeleteonline distance learning ensures a flexible schedule for learners and educators. Learners can attend lessons at their own pace and time, while educators can teach at their own convenience.
ReplyDeleteRead this blog to know about the potential benefits of AR and VR development company. These tech solutions offer zero risks, a pleasant experience, and a popular trend in the automobile sector.
ReplyDeleteWe have informed you that Fix My Lappy provides you best Hp Service Center in Noida. They have 3-4 experts with a lot of stock availability for the Noida Region. Assuming that any timetable or call grounds to us for administrations immediately back-end administration individuals started to find a good pace client and as shown by the clients need, they make their timetable?
ReplyDeletetrending technology
ReplyDeleteblogging platforms
advantages of blogging platforms
Guest Post
trending technology
United airlines manage booking facility works and help you achieve the desired tasks. The question is, how does this service assist you, and what changes can you make to it? They can rapidly make modifications to their itinerary using the united manage booking option. Most crucially, they are able to add certain service upgrades to their initial flight at a very low cost.
ReplyDeleteRead this blog to know about the potential benefits of AR and VR. These tech solutions offer zero risks, a pleasant experience, and a popular trend in the automobile sector.
ReplyDeletevisit here : AR and VR development company
I am somewhat certain I’ll be informed plenty of new stuff right here! Good luck for the following! personality development training
ReplyDeleteEvery time Peoples want some exciting ideas. If you think you are very creative and people really love your post, then you got trustworthy from used.
ReplyDeleteirish translate
Microsoft Dynamics 365 Sales is the best platform that enables best-in-class sales automation and the end-to-end management of your company development process.
ReplyDelete"Allegiant Airlines Change Flight Policy?
ReplyDeleteAllegiant Airlines Is A Low-Cost Carrier Based In The United States, Serving Over 120 Destinations Across The Country. Allegiant Airlines Change Flight If You've Booked A Flight With Allegiant Airlines, You May Need To Make Changes To Your Itinerary At Some Point. The Good News Is That Allegiant Airlines Does Have A Change Flight Policy In Place.
Allegiant Airlines' Change Flight Policy Allows Passengers To Make Changes To Their Itinerary, Including The Date And Time Of Their Flight, As Well As The Destination, For A Fee. The Fee Varies Depending On The Type Of Fare You Purchased And The Time At Which You Make The Change.
If You Need To Change Your Allegiant Airlines Flight, You Can Do So Online By Logging Into Your Account On The Airline's Website. Simply Go To The ""Manage Travel"" Section And Follow The Prompts To Make The Changes You Need. If You're Having Trouble Making The Changes Online, You Can Call Allegiant Airlines' Customer Service Center To Speak With A Representative Who Can Assist You.
"
This post is very interesting and informative thanks for sharing with us such a wonderful post. If you are a student and looking for the best nursing assignment help. Our nursing assignment expert are well-educated and professional experts and complete your assignment on time at very cheap prices.
ReplyDeleteIf you're wondering whether can you bring honey on a plane, this article will provide you with essential information on the subject. Different countries may have different regulations and guidelines, so it's best to check Can you bring honey on a plane and the customs regulations of your destination country before packing honey in your luggage.
ReplyDeleteAre you struggling with your WordPress assignments and looking for reliable online assistance? Look no further! In this comprehensive guide, we will explore the world of Online WordPress Assignment Help and provide you with valuable insights, tips, and resources to excel in your WordPress projects. Whether you're a beginner or an advanced user, this article will equip you with the necessary tools to tackle any WordPress assignment with confidence.
ReplyDelete
ReplyDeleteArticle Submission Sites
what are backlinks in seo
High PR PPT Submission Sites List 2023
Video Submission sites
Agility is essential for success in the modern business environment. Traditional offline employment frequently entails tight, long-term commitments, which makes it difficult for businesses to modify their workforce in response to changing demand. However, outsourcing provides an unmatched level of flexibility. Businesses may quickly scale up or down their teams in accordance with project demands, which enables them to save costs and react quickly to market developments. Businesses have a substantial competitive advantage because to this dynamic personnel management in today's dynamic environment. You can find out more by clicking here!
ReplyDeleteCheap flight tickets to atlanta
ReplyDeleteAssignment help differs from the majority of fields in that there is only one right response, and in that case help with assignment service offers the best resolving issues strategy for you. In order to serve as an outline for students in understanding the process, we produce an answer step by step. Our expertise is in providing online accounting coaching, and our teachers are intelligent and fully comprehend the issues that are raised in your accounting assignments.
ReplyDeleteGreat blog thank you for sharing.
ReplyDeleteGroup Therapy Online
Appreciate your well written and long article post. You done really nice work in this article. I hope in future you share more good updates. Now it's time to avail Limo’s limo service West Palm Beach for more information.
ReplyDeleteAre you curious about the Egg freezing price in delhi? Well, let me tell you, it's quite affordable! The price for this procedure varies depending on the clinic and the services offered, but you can expect to pay around INR 50,000 to INR 1,50,000. Don't worry, though, many clinics offer financing options to make it easier for you to afford. Egg freezing is a great option for women who want to preserve their fertility for the future, and with the reasonable prices in Delhi, it's definitely worth considering.
ReplyDeleteYour personal experiences really added depth to this article. It's refreshing to read a piece that combines research with personal anecdotes. Thank you for sharing your story with us. atencion a clientes american airlines
ReplyDeleteGreat article! I found the information here very insightful and well-presented. The author has a deep understanding of the topic. Visit https://astrokundli.net for similar content and free astrology services like: free kundli, free horoscope, free kundli milan and more.
ReplyDeleteQatar Airways change flight policy is designed to provide passengers with convenience and peace of mind. The clarity in guidelines and the helpful assistance from their customer support team made the transition to new travel dates straightforward. Qatar Airways' commitment to customer satisfaction shines through in their adaptable policies, making it a preferred choice for those who value flexibility in their travel plans."
ReplyDeleteIf you're looking for top-quality natural stone, then look no further than our premium collection. Our stones have been used to create stunning spaces for some of the biggest builders and developers in the USA. When it comes to pricing and value for money, our products are second to none. quartz countertops in houston
ReplyDelete
ReplyDeleteThose who are travelling with pets can be accommodated by Lufthansa extensive and flexible Lufthansa pet cargo . Depending on their size and travel needs, dogs are permitted to fly as cargo, checked luggage, or in the cabin on the airline. Larger pets can be carried in the cargo hold, while smaller dogs and cats can fly in the cabin with their owners.
Binge Contact Number Australia (611800595174) to frequently asked questions and expert tips for a seamless experience. A friendly customer support representative will be ready to assist you with any queries or concerns you may have.
ReplyDeleteWe are today leason "How To Keep Bugs Out Of House"
ReplyDeleteThe Blue Screen of Death (BSoD), a dreaded sight for every Windows user, has a long and intriguing history. Over the years, it has become synonymous with system crashes and technical malfunctions. In this article, we will delve into the evolution of the Blue Screen of Death, exploring its origins, development, and the impact it has had on the world of computing.
ReplyDeleteVisit site :
The History of the Blue Screen of Death
Soya Bean Chunks Nutritional Value, also known as textured vegetable protein (TVP) or soya chunks, are derived from defatted soy flour, making them a versatile and nutritious alternative to meat. Packed with essential nutrients, these plant-based protein sources offer numerous health benefits. First and foremost, soya bean chunks are rich in high-quality protein, containing all the essential amino acids required by the human body for muscle growth, repair, and overall health. This makes them an excellent choice for vegetarians, vegans, and anyone looking to reduce their intake of animal products while still meeting their protein needs.
ReplyDeleteSoya Bean Chunks Nutritional Value
Welcome to the ultimate guide on mastering implied odds poker Whether you're a seasoned player or just starting, understanding implied odds is crucial for success in this dynamic game of skill and strategy. In this comprehensive article, we'll delve into the intricacies of implied odds poker, exploring key concepts, advanced strategies, and practical tips to elevate your gameplay to the next level. Let's dive in!Implied odds poker is a sophisticated strategy that goes beyond the basic odds of winning a hand. It involves assessing the potential future bets and factoring them into the current decision-making process. By understanding implied odds, players can make more informed decisions about whether to call, raise, or fold, ultimately maximizing their profitability over the long term.Mastering implied odds begins with understanding how to calculate them accurately. Unlike pot odds, which consider the current size of the pot relative to the bet size, implied odds take into account the potential size of future bets. This involves estimating the likelihood of winning a hand and predicting the potential profit from future bets if you hit your draw.
ReplyDeleteRead more : ofilmywap
Users can safely import OST files into Office 365 by taking the help of a useful solution MailsDaddy OST to Office 365 Migration Tool. The software facilitates users to shift multiple OST files into one or more O365 accounts at a time. Here users can view the preview of all OST file databases before migration.
ReplyDeleteTo know more, visit here: https://www.mailsdaddy.com/ost-to-office-365-migration-tool/
Nice!
ReplyDeleteThank you for sharing
Mobile by don rocco
Great insight. As someone deeply invested in language learning, I completely agree with the points made in this blog.
ReplyDeleteAt Language Gurus, we’ve seen firsthand how access to experienced tutors can transform a student’s language journey. Our platform connects learners with seasoned language experts, offering personalized lessons that cater to individual learning styles and goals. It’s amazing how much progress can be made with the right guidance!"
This comment has been removed by the author.
ReplyDeleteA nursing student was struggling with her assignment, feeling overwhelmed by the complex topic. he didn’t know where to start or how to organize his ideas. In search of help, he found a nursing assignment writing service that offered support with detailed and well-researched content. he decided to give it a try and was amazed by the quality of the work he received. The assignment was clear, thorough, and helped his better understand the subject.
ReplyDeleteThreat hunting with Sysmon and open-source tools sounds fascinating! It's great to see how dashboards can enhance visibility and hunting efficiency. Balancing learning about security and academics can be tough thankfully, Do My Online Law Class help makes it easier to stay on track.
ReplyDeleteBuilding a Sysmon dashboard with an ELK Stack is a powerful way to visualize and analyze system monitoring data. By integrating Sysmon logs with Elasticsearch, Logstash, and Kibana (the ELK Stack), you can create a dynamic, real-time dashboard that provides valuable insights into system performance and security. If you are building a dashboard and struggling with accounting classes, consider online accounting class helpers for your guide.
ReplyDeleteAn Offer in Compromise (OIC) is a program offered by the IRS that allows eligible taxpayers to settle their tax debts for less than the full amount owed. It is designed for those who cannot pay their full tax liability or would face significant financial hardship if required to do so.To qualify, the IRS evaluates a taxpayer's ability to pay, income, expenses, and asset equity. The settlement amount is based on the taxpayer's reasonable collection potential (RCP), which considers future income and the value of assets.
ReplyDeleteTax Prep Planning For Individual
Tax Prep Planning For Medium Companies
Miyapur, located in Hyderabad, is home to several Junior Intermediate Colleges in Miyapur offering quality education to students. These institutions cater to diverse academic needs, focusing on disciplines like science, commerce, and humanities. Prominent colleges in the area emphasize a well-rounded approach to learning, blending academic excellence with extracurricular activities.Facilities like well-equipped labs, libraries, and experienced faculty help students build a strong foundation for higher education. Some colleges also provide integrated coaching for competitive exams such as JEE, NEET, and CA foundation courses, enabling students to prepare for their careers effectively. Additionally, many institutions offer affordable fee structures, ensuring education is accessible to a broader section of society.
ReplyDeleteReadmore; Top CBSE Schools in Hyderabad
Best Junior Intermediate Colleges in West Maredpally
Junior Colleges in West Maredpally
Write for us sports play a vital role in our lives, offering countless physical, mental, and social benefits. Engaging in sports not only improves fitness but also enhances overall well-being by reducing stress and promoting mental clarity.
ReplyDeleteWhen you write for us + fashion, choose your topic precisely. We appreciate well-written posts related to latest fashion trends, styles, beauty and health tips, and fashion designers from guest writers. Your post should be fresh and have not been posted anywhere on the Internet except your own platform or website.
ReplyDeletewrite for us + fashion
write for us + "fashion" The fashion industry is a constantly changing landscape full of creativity, trends, and self-expression. If you’re passionate about fashion and have a knack for writing, contributing to fashion blogs, magazines, or websites can be a rewarding experience. This guide will help you understand how to create captivating fashion content that resonates with readers, while providing valuable tips and guidelines for writing fashion-focused articles.
ReplyDeletewrite for us + "fashion"
Are you passionate about video games write for us and love sharing your insights? We’re looking for enthusiastic writers to contribute to our platform! Whether you’re an expert in football, basketball, cricket, tennis, or emerging sports, we welcome well-researched and engaging articles. Topics can include game analysis, player profiles, match predictions, fitness tips, sports technology, and more.
ReplyDeletewrite for us casino offer an exciting blend of luck, skill, and entertainment, making them a popular choice for gaming enthusiasts worldwide. Whether you prefer the spinning thrill of slot machines, the strategic depth of poker, or the fast-paced excitement of roulette and blackjack, there's something for everyone in a casino. Modern casinos provide more than just gaming—they offer luxurious resorts, fine dining, and live entertainment, creating an all-in-one entertainment hub. Online casinos have further revolutionized the industry, allowing players to enjoy their favorite games from the comfort of their homes.
ReplyDeleteIn the rapidly evolving biopharmaceutical industry, Single Use Assemblies have revolutionized bioprocessing by providing cost-effective, contamination-free, and highly efficient solutions. Foxx Life Sciences offers a wide range of high-quality Single Use Assemblies designed to meet the stringent demands of modern bioprocessing applications.
ReplyDeleteSingle Use Assemblies
Looking for premium Wall panel suppliers in Hyderabad ? We specialize in providing high-quality decorative, PVC, WPC, MDF, and 3D wall panels to enhance residential and commercial interiors. Our wall panels are designed to be durable, stylish, and easy to install, offering the perfect solution for modern decor needs. With a wide range of textures, colors, and designs, we cater to homes, offices, hotels, restaurants, and commercial spaces. Our expert team ensures customized solutions, helping you choose the best panels to suit your aesthetic and functional requirements. Whether you need soundproof, waterproof, or fire-resistant panels, we bring affordable and innovative wall solutions that transform spaces effortlessly. Trust our trusted suppliers in Hyderabad for quality materials, competitive pricing, and seamless installation services.
ReplyDeleteUr leading best digital marketing agency in hyderabad offers result-driven solutions tailored to your business needs. From SEO, social media marketing, and PPC advertising to content marketing and web development, we help businesses grow and achieve their goals.
ReplyDeleteExpedia Customer Service
ReplyDeletePassionate about tech innovation. Aiming for Blockchain Council certification. Skilled in Computer Security Certification & currently diving into Artificial Intelligence Training. Always learning, always evolving!
ReplyDeleteInformation Security Certificate || Certified Data Science Developer
3d molding design is a cutting-edge process used in product development and manufacturing to create precise and intricate mold structures in a virtual three-dimensional space. It involves using advanced CAD software to visualize, simulate, and perfect the mold before it goes into actual production. This technique allows engineers and designers to identify potential issues early, improve efficiency, and reduce production costs. At FoxxTechnologies, we specialize in delivering innovative 3D molding design solutions tailored to meet the unique needs of each project. Our expertise ensures high-quality output, accuracy, and streamlined workflows that help businesses accelerate their product development cycle with confidence and precision.
ReplyDeleteC movies 2025 is expected to be one of the popular free movie streaming platforms where users can watch the latest films, classic titles, and trending TV shows without a subscription. Known for offering a vast library of content across different genres like action, romance, horror, and drama, the platform continues to attract audiences looking for convenient online entertainment. C Movies typically allows viewers to stream content in high-definition quality with minimal interruptions, often hosting a user-friendly interface that makes it easy to search and select movies. In 2025, it remains a favored option for those seeking hassle-free streaming without the need for account creation, appealing to users who want quick and free access to a broad collection of entertainment content online.
ReplyDeleteGreat article! As a nursing student in Australia, managing clinical placements and theory work together is tough. I found amazing support through this nursing assignment help in Australia platform. Their expert guidance really helped improve my grades!
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteinterior clads are decorative surface materials used to enhance the aesthetic appeal and functionality of interior spaces. These cladding solutions come in a wide variety of textures, finishes, and materials, including wood, stone, metal, PVC, and composite panels, offering versatility for both residential and commercial interiors. Interior clads not only add visual interest but also serve practical purposes such as protecting walls from damage, improving insulation, and covering imperfections. They are commonly used in living rooms, lobbies, hallways, kitchens, and bathrooms to create stylish and contemporary environments. With growing trends in modern interior design, interior cladding has become an essential element for architects and designers aiming to achieve both elegance and durability.
ReplyDeleteLeadership Hiring is a critical aspect of building a successful organization, as it involves identifying and attracting individuals with the vision, experience, and strategic mindset required to guide teams and drive business growth. Unlike regular recruitment, leadership hiring demands a deep understanding of both the organization's long-term goals and the dynamic qualities that define an effective leader. Companies invest substantial time and resources into sourcing candidates who not only possess the right skill set but also align with the company’s culture and values. The process often includes extensive background checks, psychometric assessments, and in-depth interviews to evaluate decision-making capabilities, communication style, and leadership philosophy.
ReplyDeleteFR - Flame retardant PVC wires & cables are specially designed to resist the spread of fire and provide enhanced safety in electrical installations. These wires and cables are made with a flame-retardant PVC compound that minimizes the risk of fire propagation in case of an electrical fault or short circuit. They are widely used in residential, commercial, and industrial applications due to their ability to self-extinguish and limit the emission of toxic gases and smoke. The construction of FR PVC wires includes high-quality copper conductors that ensure excellent conductivity and durability while the flame-retardant insulation layer provides a high level of thermal and mechanical protection. These cables are ideal for use in places where fire safety is a critical concern, offering reliable performance, longer service life, and compliance with national and international safety standards.
ReplyDeleteChoosing the Best CBSE & CAMBRIDGE International School in Hyderabad involves finding an institution that balances academic excellence with holistic development. Hyderabad, being a growing hub for quality education, offers several top-tier schools that follow both the CBSE curriculum and the Cambridge Assessment International Education framework. These schools are known for their state-of-the-art infrastructure, experienced faculty, and a student-centered learning environment. With a strong focus on global exposure, critical thinking, and co-curricular engagement, such institutions cater to students aiming for both national and international academic success.
ReplyDeleteIn today’s fast-paced digital marketplace, having a professional and feature-rich eCommerce website is the key to business success. Choosing the Best Ecommerce Website Development Company can make all the difference in delivering a seamless shopping experience that attracts, engages, and converts customers.
ReplyDeleteAt honeywebsolutions, we specialize in creating high-performance eCommerce platforms tailored to your unique business needs. Our team of skilled developers, designers, and strategists ensures your online store not only looks visually stunning but also functions flawlessly across all devices.
Best Ecommerce Website Development Company
Tirupati Tourism is a popular tourist destination located in the Chittoor district of Andhra Pradesh, India. The town is famous for its world-renowned Sri Venkateswara Temple, which attracts millions of devotees from all over the world.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteStruggling with chest enlargement and self-consciousness? As a leading clinic offering Gynecomastia Surgery in Hyderabad, Dr. Divya Sai Narsingam provides expert male breast reduction treatments tailored to each individual. Through a combination of liposuction, glandular excision, and skin tightening where needed, she aims for a well-contoured, natural chest shape that restores comfort and confidence. Whether the tissue is firm glandular type or a mix of fat and skin excess, the surgery is planned with precision and performed under safe, compassionate care. With modern surgical techniques, minimal downtime, and a focus on both aesthetic outcome and functional recovery, patients can expect discreet scars, smoother chest contours, and renewed self-esteem with Gynecomastia Surgery in Hyderabad.
ReplyDeleteAre you dreaming of pursuing higher education in Germany but worried about tuition fees and living expenses? Don’t stress — Study in Germany scholarships With the right planning and guidance from experts like SquareOneOverseas, your dream of studying in one of Europe’s most advanced countries can become a reality.
ReplyDeleteWith modern surgical techniques, minimal downtime, and a focus on both aesthetic outcome and functional recovery, patients can expect discreet scars, smoother chest contours, and renewed self-esteem with Gynecomastia Surgery in Hyderabad.
ReplyDeleteWhether the tissue is firm glandular type or a mix of fat and skin excess, the surgery is planned with precision and performed under safe, compassionate care. With modern surgical techniques, minimal downtime, and a focus on both aesthetic outcome and functional recovery, patients can expect discreet scars, smoother chest contours, and renewed self-esteem with Gynecomastia Surgery in Hyderabad. vclubshop.gd
ReplyDeleteaffordable WhatsApp marketing services in Hyderabad are becoming one of the most effective ways for businesses to connect directly with their audience. With the city’s growing digital market, companies are increasingly turning to WhatsApp as a reliable communication and marketing channel. These services help businesses promote their products, send personalized messages, and engage customers instantly at a very low cost. By using affordable WhatsApp marketing services in Hyderabad, brands can reach thousands of potential customers with just one click, making it ideal for small and medium enterprises looking to expand their reach without heavy investment.
ReplyDeleteJapali Theertham Tirumala is a sacred pilgrimage site nestled deep within the lush forests of Tirumala, holding immense spiritual significance for devotees visiting Lord Venkateswara Temple. This holy theertham is closely associated with Lord Hanuman, who is believed to have meditated here while performing penance to serve Lord Rama. Surrounded by natural springs, dense greenery, and serene silence, Japali Theertham offers a divine atmosphere that attracts pilgrims seeking peace, devotion, and spiritual purification. The place is revered for its calm surroundings, making it ideal for meditation and reflection away from the bustling temple areas.
ReplyDeleteThe CAPM Certification Course Vizag is designed to help aspiring project professionals gain globally recognized project management credentials. This course offers structured learning aligned with PMI® standards, focusing on project planning, execution, monitoring, and control.
ReplyDeleteThe United States is one of the top destinations for students aspiring to pursue engineering education. With world-class universities, cutting-edge research facilities, and strong industry connections, Engineering courses in USA offer unmatched academic and career opportunities. With expert guidance from squareoneoverseas, students can confidently take the next step toward a successful engineering career.
ReplyDeletegbwhata is a helpful platform for users looking for more features than standard WhatsApp. It shares the latest GB WhatsApp APK versions with advanced privacy tools, custom themes, and flexible chat settings. The site also includes download links, update guides, and useful tips for safe installation. For a trusted and secure GB WhatsApp experience, visit https://gbwhata.net
ReplyDeleteGreat article with clear travel insights and practical booking suggestions. It’s always helpful to explore such guides before making travel decisions. A valuable resource for people looking for Flights from Brisbane to Melbourne. Flights from Brisbane to Melbourne
ReplyDeleteMedical and Scientific Communication refers to the clear, accurate, and effective exchange of complex medical and scientific information among healthcare professionals, researchers, regulatory bodies, and the general public. It plays a critical role in translating scientific data, clinical research findings, and healthcare knowledge into understandable formats that support decision-making, patient care, and public health awareness. This type of communication includes a wide range of activities such as medical writing, publication development, regulatory documentation, clinical study reports, and educational materials.
ReplyDeletemodern face sculpting options include a wide range of advanced cosmetic and non-surgical treatments designed to enhance facial contours, restore volume, and improve skin tightness with natural-looking results. Popular techniques such as dermal fillers, Botox, and fat grafting help define areas like the jawline, cheeks, and chin while reducing wrinkles and fine lines. Non-invasive procedures like radiofrequency microneedling, ultrasound therapy, and thread lifts stimulate collagen production and lift sagging skin without the need for major surgery. Additionally, treatments like laser resurfacing and chemical peels improve skin texture and tone, while facial sculpting tools and therapies enhance circulation and muscle tone for a more youthful appearance. With personalized treatment plans and advanced technology, modern face sculpting options provide effective solutions for achieving a balanced, refined, and rejuvenated facial profile.
ReplyDeleteGarage door repair near me results can vary, but guides like this help in selecting trustworthy professionals without confusion.
ReplyDeleteemergency garage door repair