The idea of Threat Hunting in an organization can no longer be dismissed. No matter how mature your organization is regarding to this concept, you might be already doing some type of hunting already. However, how do you show the effectiveness of your hunting engagements? How do you show to your senior leadership the progress of your hunt team? There is the misconception of doing it by only tracking the number of incidents uncovered during hunting campaigns. However, in my opinion, it is is also important to consider if the right data is being collected, automation is being improved, and how much the team knows about its own environment when hunting for specific adversary techniques (You can change this and create your own metrics. This is just my opinion)
In this post, I will examine the MITRE ATT&CK framework in the form of a heat map in order to measure the effectiveness of a Hunt Team. I will use Excel (VLOOKUPs formulas & Conditional Formatting features) and the MITRE ATT&CK matrix structure to show you how to build your own heat map and start measuring the effectiveness of your hunt team for free.
Heat Map Goals:
- Provide transparency to senior leadership on threat hunting strengths and weaknesses
- Perform a gap analysis to demonstrate where resources are needed in your environment
- Emphasize the effectiveness of collaboration among other teams (In order to reach a very good or excellent score, you might need to work with other teams to fill the gap)
- Prioritize techniques based on the most crucial gaps identified
MITRE ATT&CK Framework
ATT&CK is a model and framework for describing the actions an adversary takes while operating within an enterprise network. The model can be used to better characterize post compromise adversary behavior with the goal of distilling common behaviors across known intrusion activity into individual or combinations of actions that an adversary may take to achieve their goals. The TTPs described in ATT&CK were selected based on observed APT intrusions from public reporting, and are included in the model at a level of abstraction necessary for effectively prioritizing defensive investments and comparing endpoint intrusion detection capabilities. [Source]
Get your own ATT&CK Matrix in Excel
Copy the MITRE ATT&CK Matrix
- Open Excel and create a new blank workbook
- Go to the MITRE ATT&CK techniques page and highlight the whole Matrix table
- Copy (CTRL + C) the highlighted table (make sure you highlight the whole table) and paste it (First cell A1 or R1C1) on your new blank workbook as shown in figure 1 and 2 below. Even though you paste it on the first row, it is pasted starting on the second one. Just delete the first row.
 |
| Figure 2: Copying Matrix to Excel |
Edit your Matrix Table
Remove Hyperlinks from the whole table at once as shown in figure 3 below. Your table might not have borders anymore so just highlight your whole table and add borders to it as shown in figures 4, 5 and 6 below.
 |
| Figure 3: Remove Hyperlinks |
 |
| Figure 4: Table without Hyperlinks |
 |
| Figure 5: Add "All Borders" to your table |
 |
| Figure 6: Plain MITRE Matrix table |
Once you have everything as a table again, you will notice that several cells have long text that needs to be wrapped into several lines to fit better. Highlight your table again and use the "Wrap Text" option as shown in figure 7 below.
 |
| Figure 7: Wrapping up long-text |
Now, the table should be ready to be used for our heat map. Add colors to your header, adjust the font size, etc. Save your document and give your worksheet a name. I named mine "HeatMap" as shown in figure 8 below.
 |
| Figure 8: Matrix Ready for our Heat Map |
UPDATE 09/10/2017: Get your own ATT&CK Matrix in Excel
- I developed a PowerShell script that I named Invoke-ATTACKAPI which leverages the MITRE ATTACK API to interact directly with the MITRE ATTACK framework and pull valuable information all at once.
- I use this script now to update my ATTACK Enterprise Matrix
- All you need to do is run the following command to get the same results as above:
Invoke-ATTACKAPI -Matrix | select Persistence, 'Privilege Escalation', 'Defense Evasion','Credential Access',
Discovery, 'Lateral Movement', Execution, Collection, Exfiltration, 'Command and Control' |
Export-Csv C:\documents\matrix.csv -NoTypeInformation
Define Your Scoring System
You need to define your scoring system and set specific criterias that you would like to use to measure how effective your team is at detecting specific adversary techniques.
A few basic steps:
- You can start by setting your rating system levels (None, Poor, Fair, Good, Very Good & Excellent).
- You can then assign a color to each score (Keep in mind you are creating a heat map).
- Map a number to each level (0,1,2..5) as shown in figure 9 below.
- Finally assign key focus points for each level. One example could be what I show in figure 9 below.
As I mentioned at the beginning of this post, tracking how many incidents get uncovered during a hunting campaign should not be considered as the ONLY indicator of an effective hunt team. Why? What if you do not find anything? Does that mean that your team is not good?. In my opinion, validating the detection of a specific adversary technique by focusing on having right data, improving the automation of hunting procedures, and knowing your environment should be also considered when determining the effectiveness of a hunt team. For example, you can focus on the following key points (This is a basic example. I recommend you come up with your own ones):
- None:
- Not enough data to detect a specific adversary technique (i.e. hunting with only Windows Security Event Logs when hunting for PowerShell activity). Also, not centralizing the amount of data needed to hunt across the whole enterprise.
- Poor:
- Sending all your logs to a central repository. If you "hunting" on one endpoint at the time, you are NOT being effective at all ! (Consider Splunk, ELK, etc)
- Creating basic signatures or correlation rules to detect specific activity. Usually this is done by correlating two to three events. Also, here is where you might have Threat Intel feeds helping your routine hunts (IOC Sweeps).
- Running queries and trying to make sense of the data without automating certain hunting procedures that could make your hunt more effective and efficient. (i.e. After running a few queries in your SIEM you might still have thousands or hundreds of events that you will still need to go through and maybe correlate them with other events to find outliers)
- Fair:
- Collecting the right data (NOT JUST MORE DATA) to improve the detection of an adversary technique. Here is where you start adding Sysmon Logs, ETW, PowerShell logs, netflow, etc). Without the right tools or processes to aggregate and make sense of all the data, your team might not be effective yet. Hunters might be running queries and still get a very high amount of events that still need to be filtered to reduce the amount of data that needs to be analyzed.
- Good:
- Correlating and integrating numerous data types across all your endpoints in order to filter out noise and potential false positives. Here is where you star using a few basic Data Science techniques in order to make sense of all the data that you have in your central repository (Better Automation)
- Very Good:
- Leveraging more than just simple outlier detection techniques. Here is where your team starts using advanced data science techniques to detect the known and unknown (Of course, data science concepts such as Machine Learning cannot be applied to every single use case or technique that you are trying to detect. If you can validate the detection of an adversary technique by just applying basic data science techniques, then you might be already in the "Very Good" level.
- Excellent:
- Here is where your team is very proficient at everything above and very effective at detecting adversary techniques, but with also a very good understanding of the environment (Beyond just having the right automation and data. If you do not understand exactly how certain activity relates to your environment then you might be missing stuff).
Remember that the table below needs to be created on a new sheet in the same Workbook where you created your ATT&CK Matrix. ( I named mine "Score Defs")
 |
| Figure 9: Basic Scoring System table |
Define each Adversary Technique
Set your own "All Techniques" Page
- Go to the MITRE ATT&CK "All Techniques" page and highlight the whole table (Same way how you did it with the matrix earlier)
- Copy (CTRL + C) the highlighted table (make sure you highlight the whole table) and paste it (First cell A1 or R1C1) on a new sheet in the same workbook.
- You will basically have to do the same adjustments you did to the MITRE ATT&CK matrix (wrap-text, font size, All Borders, Remove Hyperlinks, etc).
- Make sure you go over the whole table and adjust certain parts of the table that might have not copied properly.
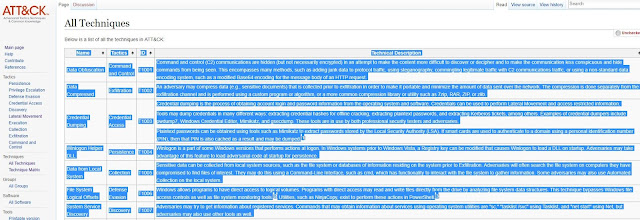 |
| Figure 10: "All Techniques" Page |
Once you have a table with everything from the "All Techniques" page, then you will have to add a few columns to add more context to it and integrate it with your Heat Map.
- I added two columns, one named "Detection Approach" and another one named "Data Sources". In the MITRE ATT&CK "All Techniques" page, I clicked on every single technique and grabbed the Detection approach and data sources needed to help me detect the specific technique.
- I also Added another one named "Detection Score". Here you will have to review one by one with your team and give it a score following your "Score Defs sheet" (None, Poor, Fair, Good, Very Good, Excellent).
- Finally, I added a column named "Tools". I use this to identify what current tools would help me hunt for a specific adversary technique. This is very helpful to also show vendors how much they are contributing to your detection/hunting capabilities (Vendors selling you EDR maybe?).
 |
| Figure 11: All Techniques Table |
UPDATE 09/10/2017: Define each adversary technique
- I developed a PowerShell script that I named Invoke-ATTACKAPI which leverages the MITRE ATTACK API to interact directly with the MITRE ATTACK framework and pull valuable information all at once.
- I use this script now to update my adversary technique sheet
- All you need to do is run the following command to get the same results before adding 'Detection Score' And tools columns:
Invoke-ATTACKAPI -Category -Technique | select @{Name="Name"; Expression={$_.Name -join ","}}, @{Name="Tactic"; Expression={$_.Tactic -join ","}}, @{Name ="ID"; Expression={$_.ID -join ","}}, @{Name="Description"; Expression={$_.Description -join ","}}, @{Name="Analytic details"; Expression={$_.'Analytic Details' -join ","}}, @{Name="Data Source"; Expression={$_.'Data Source' -join ","}} | export-csv F:\wardog\scripts\techniques.csv -NoTypeInformation
Set a Detection Score Drop-Down List
I added a "Detection Score" column and was able to assign a score to each technique. What if we want to change the score? Do we delete the text and type it again?. I recommend to use n Excel feature named "Data Validation" under the "Data" tab. This limits the type of data that can be entered in a cell. This will help us to have a drop-down menu to pick from the 6 different levels of the rating system.
- Highlight all your Detection score cells, click on the tab named "Data", and on "Data Validation" as shown in figure 12 below.
- A window will pop up where you will have to select the list of values that you will want to use as part of your drop-down menu.
- Click inside of the "Source" box and then click on the "Score Defs" sheet. Highlight the six levels (None, Poor, Fair, Good, Very Good, Excellent) and click Okay as shown in figure 14 below.
- You will be able to now just hover over the right edge of the cells below the "Detection Score" column and you will have 6 options as shown in figure 15 below.
 |
| Figure 12: Highlighting "Detection Score" cells |
 |
| Figure 13: Selecting a Source list |
 |
| Figure 14: Getting values from the Score Defs sheet |
 |
| Figure 15: Drop-Down list enabled on Detection Score cells. |
Integrate All the Sheets
Heat Map Sheet: Add Scoring Columns
Add a blank column to the right of each tactical group as shown in figure 16 below. There is where you will sync the score you set for each technique in the "Detailed Technique" sheet.
 |
| Figure 16: Adding extra columns to the Heat Map. |
Heat Map Sheet: VLOOKUPS
If your Excel version sets your Columns to be numbers instead of being letters, then you have the R1C1 reference style option enabled by default. If you are not comfortable with the R1C1 Reference style of your table, then you need to disable that feature by going to File> Option > Formulas ,un-check R1C1 reference style feature and click OK as shown in figure 17 below.
 |
| Figure 17: Disable R1C1 Reference Style |
Now you should be good to start setting your VLOOKUP formulas. First, Highlight the first cell next to the first Persistence technique ("Accessibility Features").
Copy the text below into the Formula bar as shown in figure 17:
=VLOOKUP(VLOOKUP(A2,'Detailed Techniques'!A:G,7,0),'Score Defs'!A:B,2,0)
- A2 is the cell to the left of the cell you highlighted (The Adversary Technique). That's the value we are going to be looking for first.
- ''Detailed Techniques'!A:G,7,0)
- The first value in quotes is the name of the Sheet where you will look value in cell A2.
- !AG: Table Range
- The second value after the comma (7) is the "Detection Score" column number where we will collect the score value for the specific adversary technique that we were looking for (A2 = Accessibility Features)
- The last value after the last comma (0) and before the ")" is basically saying "Match the exact value" that I am looking for (not fuzzy matching).
- 'Score Defs'!A:B,2,0)
- The first value in quotes again is just pointing to the "Score Defs" sheet where you will now look for the Score string retrieved from the "Detailed Technique" sheet.
- The second value after the first comma (2) is the "Integer Mapping" column number where we will collect the value (number) in relation to the specific score level (None, Poor, Fair, Good, Very Good or Excellent).
- The last value after the last comma (0) and before the ")" is basically saying "Match the exact value" that I am looking for (not fuzzy matching).
As you can see below, after entering the formula from above, I got a value of Zero which means that I set the score for Accessibility Features to be "NONE" ( Not data available for that technique)
 |
| Figure 18: Double VLOOKUP to get a score value for each technique |
Now in order to test your formula with other techniques in the same column, select the cell with the number "0" and drag the bottom right corner of the cell down to apply the same formula to all the columns below as you can see in figure 19 below.
 |
| Figure 19: Double VLOOKUP to get a score value for each technique |
There will be cells that will be just blank, and in order to not get any error messages, we just have to add a conditional to the formula. Replace the first formula with the following:
=IF(ISNA(VLOOKUP(VLOOKUP(A2,'Detailed Techniques'!A:G,7,0),'Score Defs'!A:B,2,0)),"",VLOOKUP(VLOOKUP(A2,'Detailed Techniques'!A:G,7,0),'Score Defs'!A:B,2,0))
 |
| Figure 20: Double VLOOKUP with IF conditional to show empty cells where there are not techniques. |
Heat Map: Locking Cell Values in Formula
Next, we have to copy the same formulas to the other columns and we want to make sure that our table ranges from our "Score Defs" and "Detailed Techniques" stay the same. The only value that should change is value of the first cell to the right of each technique. You can lock parts of your formula by doing the following:
- Click on the first cell where you created the firs formula (B2)
- Place your cursor on the Table Range of each sheet and press F4
- You will see the table range values with Dollar Signs next to their parameters as shown in figure 21 below.
 |
| Figure 21: Lock cell values |
Then, copy the first cell to the right of "Accessibility Features" under persistence, and paste it at the beginning of each column to the right of each technique. Then, drag the bottom right corner of each cell with the formula down until the last technique of each column as shown in figure 22 below. You will see that every single technique now has a value associated to its rate level.
 |
| Figure 22: All the values from the Detailed techniques and Score Defs are synced |
Add Colors to your Heat Map
Get your RGB Color Values
First get the RGB values of all your rate levels. You can do that by going to your "Score Defs", clicking on the rate cell and checking its "More colors" settings of the fill color as shown in figure 23 below. Do the same for every single color. Let me share my RGB values just in case you like mine:
0 = RGB 255 79 79
1 = RGB 255 119 87
2 = RGB 255 174 93
3 = RGB 242 245 123
4 = RGB 209 220 255
5 = RGB 125 156 255
 |
| Figure 23: RGB Value of Poor/1. |
Conditional Formatting: Creating Rules
Once you have all your RGB values written down, go to your "HeatMap" sheet and highlight the whole table. Do the following:
- Click on Conditional Formatting > New Rule as shown in figure 24 below
- Select "Use a formula to determine which cells to format" (Figure 25)
- In the "Format values where this formula is true", type: =B2=1 (Figure 26)
- Click on Format > More Colors> and set the RGB value for the Rate Poor=1.
- Click OK> OK > OK (Figure 27)
- You should now see all the techniques where the effectiveness of the Hunt team was set to 1 as orange as shown in figure 28
 |
| Figure 24: Creating a new rule. |
 |
| Figure 25: Setting the rule type. |
 |
| Figure 26: Set the values where the formula is true. |
 |
| Figure 27: Setting the RGB value.. |
 |
| Figure 28: Poor values. |
Next, create the rest of the rules for the rate values of 2, 3, 4 , 5, 0 and "" (BLANK) Yes you have to create a BLANK rule at the end. Make the "" rule your last rule and set it to "No color" (The rule should show up as the first top rule). That rule should look like something like this: =B2="" .
Once you have all the rules in place, your heat map should look like this:
 |
| Figure 29: Your First Heat Map. |
Bonus: Effectiveness Trend
You can add up all the values per tactical group, get the average number and show a chart with a summary of how effective your hunt team is per tactical group and per quarter. (Your Boss will love this)
 |
| Figure 30: Effectiveness Trend Over Time. |
Test your Heat Map: Take Care of the Basics
Lets say you start sending all your native windows event logs to a central repository and start collecting Sysmon logs too. You will see techniques going from None to Poor or Fair (This is just an example). Remember that even though we might have some extra visibility, you still would have to go through a lot of data and analyze several events if you do not improve the automation of certain hunting procedures. Several adversary techniques require more than just a simple correlation rule or signature. Also, we are measuring the effectiveness of the Hunt Team and not just how many incidents get uncovered during the hunting campaign.
 |
| Figure 31: Heat Map update |
Final Thoughts
I hope this was very helpful for those Hunt Teams that would like to give themselves an idea of how effective their hunt team is. This is one of many ways that you can put metrics towards your hunting campaigns.
For those that would like to just download the template and start using it right away, you can find it in the metrics folder of the ThreatHunter-Playbook
URL: https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/blob/master/metrics/HuntTeam_HeatMap.xlsx
if you would like to contribute to the ThreatHunter-Playbook, just send a PR !
Feedback is greatly appreciated! Thank you.


In the section "Test your Heat Map: Take Care of the Basics" are your scores going from None to Poor to Fair automatically? I read through this article a few times and did not see how you would automate the rating of these scores.
ReplyDeleteHey Thank you for the question. I was actually thinking on adding an extra image in there to show how to update the scores but I thought it was already being taken care of when I showed how to create the drop-down menu in figure 15. Every time you simulate and validate the detection of a technique, you and your team will have to manually update the detection score of the specific technique. You will just have to go to the "Detailed Techniques" Sheet, look for the specific technique and change the value of the cell under the "Detection Score" Column (None, Poor, Fair, Good, Very Good, & Excellent). I hope this answers your question. Let me know if this helped. Thank you !
DeleteThanks for the quick reply. It does help
Delete
DeleteBuy Adderall, Ambien, Xanax, Oxycontin Online at Walgreens Pharmacy
Order Brand & Generic Meds Online at Online Xanax Shop
Buy Xanax Online
Order Xanax Online
Buy Oxycodone Online
Buy Ambien Online
Buy Adderall Online
Order Adderall Online
buy hydrocodone online
Deletebuy hydrocodone online without prescription
buy hydrocodone online no prescription
can you buy hydrocodone online
how to buy hydrocodone online
where to buy hydrocodone online
buy hydrocodone online with credit card
can i buy hydrocodone online
where can i buy hydrocodone online
Awesome.. tnx a lot..
ReplyDeleteThank you for the feedback vishnu! I hope it helps :)
DeleteHi CyberWarDog,
ReplyDeleteI enjoyed your blog, especially because it doesn't rely on splunk, but Kibana. This helped to improve our monitoring.
So here's my question:
I've implemented a USB HID backdoor for a Pi Zero to get access to air gapped machines. I'm interested in your ideas about triggered IOCs you see in the attack.
Everything is PowerShell and NET based. I avoided using parameters like "-exec bypass", "-NoP" etc.
Considering "Module Logging", the main part of the payload is loaded as NET assembly, only stage 1 uses PowerShell commands. "IEX" is used one time, but this is optional. Nothing is written to disc. The powershell parts calling kernel.dll or user32.dll code use reflections, in order to avoid compiling CSharp inline code (and thus writing temporary files to disc).
Details could be found here: https://github.com/mame82/P4wnP1/blob/master/README.md
Hey Mame82, I am very happy to hear that I could help a little bit with your monitoring :) . I am sorry for my late response. Regarding triggered IOCs by your interesting USB HID backdoor, I would say that without testing yet, I think that from a powershell perspective you will still show in the module logging logs because of the reflection technique being used to avoid compiling Csharp. I will take a look at it and provide more details. Thank you for sharing your feedback! I cant wait to test your tool. I hope you have a great weekend!
DeleteThanks so much for this. When I try:
ReplyDeleteInvoke-ATTACkAPI -Category -Technique | select Name, Tactic, Description, 'Analytic Details', 'Data Source' | export-csv -Notypeinformation C:\Documents\techniques.csv
I get a csv full of System.Object[] for every column except "Tatic". Running the command without the export-csv, the output shows the data is there just fine.
Is this to do with the String casting that runs as part of the export-csv? Or am i missing something obvious?
Answered my own question with some code from your github readme:
DeleteInvoke-ATTACKAPI -Category -Technique | select @{Name="Name"; Expression={$_.Name -join ","}}, @{Name="Tactic"; Expression={$_.Tactic -join ","}}, @{Name ="ID"; Expression={$_.ID -join ","}}, @{Name="Description"; Expression={$_.Description -join ","}}, @{Name="Analytic details"; Expression={$_.'Analytic Details' -join ","}}, @{Name="Data Source";Expression={$_.'Data Source' -join ","}} | export-csv -NoTypeInformation techniques.csv
Hey Scotty! Sorry for the late response, I just got back from my honeymoon. I updated the post with the example from the github readme. Thank you for double checking. Thank you for the feedback too. I really appreciate it. Would you mind sharing how you are using the heatmap?? I would love to hear new ideas and how it can be improved. Thank you again!
DeleteSure thing - what's the best way to get in touch to have a chat?
DeleteHey Scotty! I hope all is well. via twitter would work first. We can discuss another channel via DM.
DeleteJust stumbled onto this, great post. I'm going through a similar effort and have a few thoughts - can discuss on twitter if easier (@ClayDoesSec);
ReplyDelete1. Open to inputs/additions to the DataSource Tool Coverage list?
2. Similar to 1, I believe there could be an expansion to prevention and response capabilities. It would manifest itself as part of the Tool Coverage list, and then potentially adding definition to the heatmap (either as contributions of the single value, or potentially their own heatmaps dedicated to protect-only and detect-only capabilities).
3. Have you already started to incorporate the ATT&CK updates from 1/16/2018?
4. Have you considered including PRE-ATT&CK?
If you are suffering from muscle spasms, then visit wayrightmeds.com to get medication online of muscle spasms. You may also buy these products by clicking these below links.
DeleteBuy Carisoprodol Online
Buy Carisoprodol 350mg Online
Buy Flexeril Online
Buy Flexeril 5mg Online
Buy Flexeril 10mgOnline
Buy Soma Online
Buy soma 250mg online
Buy soma 350mg online
ReplyDeleteIt is nice blog Thank you provide important information and i am searching for same information to save my time Data Science online Training India
buy hydrocodone online
Deletebuy hydrocodone online without prescription
buy hydrocodone online no prescription
can you buy hydrocodone online
how to buy hydrocodone online
where to buy hydrocodone online
buy hydrocodone online with credit card
can i buy hydrocodone online
where can i buy hydrocodone online
This comment has been removed by a blog administrator.
ReplyDeleteThis comment has been removed by a blog administrator.
ReplyDeleteThis comment has been removed by a blog administrator.
ReplyDeleteHey! Someone in my Facebook group shared this site with us so I came to check it out. I’m definitely enjoying the information. I’m bookmarking and will be tweeting this to my followers! Excellent blog and terrific design and style.
ReplyDeleteAlfred
Hi CyberWardog - the link to the heatmap.xlsx seems to be broken. Could you provide an alternate way to download? Much appreciated. The work you have done is awesome!
ReplyDeletei am always like to learn hunting resources. today i got here some issue about this topic, great explanation. thanks. i also tried to start hunting resources, just check it
ReplyDeleteGet Mutual Fund Investment Schemes by Mutual Fund Wala and know about the best investment platform for you, to get profit.
ReplyDeleteBest Performing Mutual Fund
Escorts in Lahore
ReplyDeleteVIP Escorts in Lahore
Escorts in Islamabad
Escorts Service Karachi
Escorts Services Karachi
Escorts in Karachi
Karachi Escorts
Call Girls in Islamabad
Escorts in Pakistan
Very informative blog post. This blog clearly shows the importance of heat mapping website. Thanks for sharing
ReplyDeleteMagnificent data, visit our page way of life magazine to get the best style and way of life magazines.
ReplyDeleteLifestyle Magazine
This is really nice, thanks again for this wonderful and valuable information sharing with us. Visit Kalakutir for Godown Floor Marking Painting and Base Company Logo Painting.
ReplyDeleteBase Company Logo Painting
thanks to sharing your article. Selenium Training In Chennai
ReplyDeleteSelenium Training In Chennai
Selenium Training In Chennai
Selenium CourseIn Chennai
Selenium Training Institute In Chennai
Best Selenium Training Institute In Chennai
Data Science Training In Chennai
Machine Learning Course In Chennai
Data Science Course In Chennai
Protractor Training in Chennai
jmeter training in chennai
Rpa Training Chennai
Cannabis, also known as marijuana among other names, is a psychoactive drug from the Cannabis plant used for medical or recreational purposes. The main psychoactive part of cannabis is tetrahydrocannabinol, one of the 483 known compounds in the plant, including at least 65 other cannabinoids
ReplyDeletebuy real weed online
how to buy weed online
buy legal weed online
buy recreational weed online
buy weed edibles online
can i buy weed online
buy medical weed online
buy weed online canada
buying weed online reviews
buy weed online legit
buy weed online without medical card
buy weed seeds online canada
order marijuana online
order marijuana seeds online
how to order marijuana online
order marijuana online without a medical card
can you order medical marijuana online
order marijuana online
Shopclues winner list 2020 here came up with a list of offers where you can win special shopclues prize list 2020 by just playing a game & win prizes.
ReplyDeletehere you can check more information:
Shopclues prize list 2020
Shopclues lucky draw
Shopclues lucky draw 2020
Shopclues prize department
Shopclues prize department 2020
great very informative....
ReplyDeleteInterview Question for CTS Placement
Cognizant Interview Questions For Fresher
Cognizant Interview Questions
Resume Coustomer Service Executive
Resume For Bank Job
Resume Cyber security Engineer
Resume Data Base Developer
Resume DeputyManager
Resume Design Engineer
Resume Desktop Support Engineer
Awesome blog. I enjoyed reading your articles. This is truly a great read for me. I have bookmarked it and I am looking forward to reading new articles. Keep up the good work!
ReplyDeletedata analytics courses
data science interview questions
business analytics course
data science course in mumbai
Buy Death Star
ReplyDeleteBuy Green Crack
Buy Zkittlez
Buy Ghost Train Haze
Buy Gorilla Glue
Buy Purple Kush
Buy Grape Ape
Buy Moonrocks
ReplyDeleteBuy Platinum Kush
Buy Lemon Kush
Buy Mango Kush
Buy Agent Orange
Buy Fire Og
ReplyDeleteBuy Death Star
Buy Green Crack
Buy Zkittlez
Buy Ghost Train Haze
Buy Gorilla Glue
Buy Purple Kush
Buy Grape Ape
very nice
ReplyDeletehttps://longislandfloorsanding.net/
http://www.diamondwoodfloor.com/
https://www.diamondwoodfloors.net/
If you are feeling very depressed, have any panic disorders, Mental Stress, Anxiety Disorders visit the page and resolve all these problams and also New Year Offer begain offer limited period.
ReplyDeleteCall Now For Buy Anxiety Medicines at very cheap price as compair to other dealer: +1-850-424-1335
Website: https://redditpharma.com/product/adderall-dosage/
https://redditpharma.com/product/ambien-dosage/
https://redditpharma.com/buy-alprazolam-online/
https://redditpharma.com/buy-hydrocodone-online/
https://redditpharma.com/buy-oxycodone-online/
https://redditpharma.com/buy-codeine-online/
topmedsreview: Provide the best information about anxiety, panic disorder, mental stress, depression, Hyperactivitys issuse. Top meds review is a social platform providing the best medical information, medicine review, and health guidance. Our website provides credible information, depth reference material about health subjects that matter to everyone.
ReplyDeleteAnxiety Medicines
Soma Addiction
Types Of Xanax Bars
Pain Relief
Really nice way to present your blog and information is also too good. Thanks for sharing it. If you are searching for more courses than visit here:-
ReplyDeleteSocial Media Marketing course
android application development
big data analytics courses
certified ethical hacker certification
open school
python class
web design classes
mobile app development training
internships near me
cyber security internships
It's really a nice experience to read your post. Thanks for sharing your innovative ideas to our vision.
ReplyDeleteData Science Course
Data Science Course in Marathahalli
We are passionate pet lovers especially dogs and cats. At impetlover, we cover from Pet Resources, Gifts Guide, How to, Informational and everything else about their breeds and tricks.
ReplyDeleteReally Very helpful Post & thanks for sharing & keep up the good work.
ReplyDeleteOflox Is The Best Digital Marketing Company In Dehradun Or Website Design Company In Dehradun
In the section "Test your Heat Map: Take Care of the Basics" are your scores going from None to Poor to Fair automatically? I read through this article a few times and did not see how you would automate the rating of these scores.
ReplyDeleteaccent pillows for sofa
burlap home decor ideas
housewarming gifts for men
This is more helpful for find the online Sexy G-Strings
ReplyDelete
ReplyDeleteThis is a wonderful article, Given so much info in it, These type of articles keeps the users interest in the website, and keep on sharing more ... good luck.
data analytics courses
Cyberops is India’s leading organization in the field of Information security.
ReplyDeleteAdvancement in technology and interconnected business ecosystems has combined to increase exposure to cyber attacks. We aim to digitally shield cyberspace by offering various products and services. We are hovering to influence our proficiency and global footprint in the field of information security and cyber crime investigation.
We foster certified training on Information Security and provide penetration testing for security audits, and Cyber Crime Investigation services for various sectors to meet their specific needs.
Our main services :
VAPT, Penetration Testing & Summer Internship in Jaipur
good blog
ReplyDeleteAI course in mumbai
Really nice and interesting post. I was looking for this kind of information and enjoyed reading this one. Keep posting. Thanks for sharing.....data science courses
ReplyDeleteI am bookmarking your article so I can revisit and review more of your content. I agree with many of your thoughts and am impressed with your out-of-the box thinking.
ReplyDeleteSAP training in Mumbai
Best SAP training in Mumbai
SAP training institute Mumbai
I concur with huge numbers of your musings and am dazzled with your out-of-the container thinking.
ReplyDeleteSAP training in Kolkata
Best SAP training in Kolkata
SAP training institute in Kolkata
I like viewing web sites which comprehend the price of delivering the excellent useful resource free of charge. I truly adored reading your posting. Thank you!...artificial intelligence course in bangalore
ReplyDeleteCan you make a video on this please? I know you had given very detailed steps but if you dont mind pls do make video. Thank you for a wonderful blog.
ReplyDeleteThanks a lot very much for the high your blog post quality and results-oriented help. I won’t think twice to endorse to anybody who wants and needs support about this area.
ReplyDeleteRobotic Process Automation (RPA) Training in Chennai | Robotic Process Automation (RPA) Training in anna nagar | Robotic Process Automation (RPA) Training in omr | Robotic Process Automation (RPA) Training in porur | Robotic Process Automation (RPA) Training in tambaram | Robotic Process Automation (RPA) Training in velachery
The Blog is really informative. every concept should be very neatly explained.
ReplyDeleteData Science Training Course In Chennai | Data Science Training Course In Anna Nagar | Data Science Training Course In OMR | Data Science Training Course In Porur | Data Science Training Course In Tambaram | Data Science Training Course In Velachery
I was just browsing through the internet looking for some information and came across your blog. I am impressed by the information that you have on this blog. It shows how well you understand this subject. Bookmarked this page, will come back for more....Data Analyst Course
ReplyDeleteAmazing Content Writing also Design of Full Deep Details best crossbow for bolts Next time Recommended Sharing Articles
ReplyDeleteI was just browsing through the internet looking for some information and came across your blog. I am impressed by the information that you have on this blog. It shows how well you understand this subject. Bookmarked this page, will come back for more....artificial intelligence course
ReplyDeletecomputer classes for beginners near me
ReplyDeleteAfter reading your article I was amazed. I know that you explain it very well. And I hope that other readers will also experience how I feel after reading your article.
ReplyDeleteData Analyst Course
After reading your article I was amazed. I know that you explain it very well. And I hope that other readers will also experience how I feel after reading your article.
ReplyDeleteartificial intelligence course in bangalore
Thanks for provide great informatic and looking beautiful blog, really nice required information & the things i never imagined and i would request, wright more blog and blog post like that for us. Thanks you once agian
ReplyDeletename change procedure in chandigarh
name change procedure in delhi
name change procedure mumbai
name change procedure in jaipur
name change in pune
online name change
name change in india
name change procedure in bangalore
name change procedure in rajasthan
name change procedure in maharashtra
Therefore, you can opt for the right institute to take a course and gain more knowledge in the field. This will help you gain the expertise and get better at what you do. 360DigiTMG data science training in hyderabad
ReplyDeleteIf you want to know about What is muscle spasms?, What is the treatment muscle spasms?, How the Skeletal Muscle Relaxer Flexeril Works? then read this informative blog...
ReplyDeleteHow the Skeletal Muscle Relaxer Flexeril Works?
Causes of muscle spasms
Buy Flexeril Online
know about Methadone And How Does It Work?, What are the side effects associated with using Methadone? then visit our website anxietymeds.org
ReplyDeleteWhat is Methadone?
Buy Methadone Online
White collar crime: this is a non-violent crime that is done by skilled professionals. As a cyber crime student you will focus on computer fraud. cyber security institute in hyderabad
ReplyDeleteknow about Is Xanax an Antidepressant,Is Xanax a Depressant? Visit our website:anxietymeds.org
ReplyDeleteSide Effects of Xanax
Buy Xanax Online
Tramadol For Pain: Side Effects, Dosages, Treatment, Interactions, Warnings
ReplyDeletefeeling sleepy, tired, dizzy or "spaced out".
constipation.
Serious side effects.
thanks to sharing your article.
ReplyDeletepython training in bangalore | python online training
aws training in bangalore | aws online training
artificial intelligence training in bangalore | artificial intelligence online training
machine learning training in bangalore | machine learning online training
blockchain training in bangalore | blockchain online training
uipath training in bangalore | uipath online training
Dangers of Xanax Bars: Alprazolam Pills Identifier
ReplyDeleteGreen Xanax Bar.
Yellow Xanax Bar.
White Xanax Bar.
Pink Xanax Bar.
Lockdown is running in the whole country due to coronavirus, in such an environment we are committed to provide the best solutions for QuickBooks Support Phone Number.
ReplyDeleteContact QuickBooks technical Support Phone Number to get in touch.
Dial QuickBooks Toll free Number : 1-844-908-0801
Attention Deficit Hyperactivity Disorder: Diagnosing ADHD
ReplyDeleteHyperactivity-Impulsivity.
Inattentive Adhd.
children and adults.
Thanks for sharing great information!!
ReplyDeleteData Science Training in Hyderabad
I think about it is most required for making more on this get engageddata science courses in malaysia
ReplyDeleteHi! This is my first visit to your blog! We are a team of volunteers and new initiatives in the same niche. Blog gave us useful information to work. You have done an amazing job!
ReplyDeletedata science course
business analytics course
data analytics course
I have recently started to read this blog, the info you provide on this post has helped me a lot. Thanks for all of your time & work.Learn Best Data Science Course in Hyderabad
ReplyDeleteI’m excited to uncover this post. I need to to thank you for ones time for this particularly fantastic read!! I definitely really liked every part of it and i also have you saved to fav to look at new information in your site.Learn Best Data Science Training in Hyderabad
ReplyDeleteI think this is an informative post and it is very useful and knowledgeable. therefore, I would like to thank you for the efforts you have made in writing this article.
ReplyDeleteData Science Course in Bangalore
Wonderful blog post. This is absolute magic from you! I have never seen a more wonderful post than this one. You've really made my day today with this. I hope you keep this up!
ReplyDeleteData Science Training in Bangalore
This website and I conceive this internet site is really informative ! Keep on putting up!
ReplyDeleteData Science Course
You completely match our expectation and the variety of our information.
ReplyDeleteData Science Training
Very impressive and interesting blog found to be well written in a simple manner that everyone will understand and gain the enough knowledge from your blog being more informative is an added advantage for the users who are going through it. Once again nice blog keep it up.
ReplyDelete360DigiTMG Machine Learning Course
Amazing post found to be very impressive while going through this post. Thanks for sharing and keep posting such an informative content in forthcoming as well.
ReplyDeleteData Science Course in Raipur
Information was spot on the topic discussed great work thank you.
ReplyDeleteData Analytics Certification Training 360DigiTMG
Buy Meds Online
ReplyDeleteBuy adderall overnight
Buy Meds Online
Buy adderall overnight
Buy Meds Online
Buy adderall overnight
I was looking for some decent stuff on the subject and have had no luck so far. You just had a new big fan! ...
ReplyDelete360DigiTMG Business Analytics Course in Bangalore
ReplyDeleteThis post is incredibly simple to examine and recognize without disregarding any nuances. Inconceivable work!
data science course in delhi
Buy Ativan online from New York
ReplyDeleteBuy Modafinil without a prescription
How to Buy Ambien without a prescription
Buy Lexapro online legit
Buy ambien online fedex
Best online pharmacy for Methadone
Buy Vicodin online overnight delivery
Buy Gabapentin Online
ReplyDeleteBuy OxyContin prescription cost
Buy opana online pharmacy
Buy Dilaudid online legally
order norco online with prescription
Buy strattera online without script
Buy Flexeril online cod
ReplyDeleteBuy Roxycodone overnight
It is a great pleasure to read your message. It's full of information I'm looking for and love to post a comment that says "The content of your post is amazing". Excellent work.
ReplyDeleteArtificial Intelligence Course in Bangalore
Eco-friendly Sustainable Hemp Products
ReplyDeleteEco-Friendly Hemp Clothing, Backpacks, Soaps, Pet Supplies, CBD Tinctures and Wellness Products
Buy Best CBD Products
Buy Best CBD Products
Buy Best CBD Products
Buy Best CBD Products
Buy Best CBD Products
Somebody Sometimes with visits your blog normally and prescribed it as far as I can tell to peruse too.
ReplyDeleteartificial intelligence courses in delhi
get more info....
ReplyDeletemore
https://www.seekace.com/about
ReplyDeletebest data science course provides by SeekACE Solutions into an emerging leader for product development and customization with a strong blend of Data Science and AI.
https://www.seekace.com/about
Is your device shows Roku Error Code 018 ? Are you looking for Roku helpline number for instant solution? Don’t get panic. Just grab your phone and dial Roku helpline number for instant solution USA/Canada: +1-888-480-0288 & UK: +44-800-041-8324. Get in touch with us.
ReplyDeletehttps://www.seekace.com/
ReplyDeleteFrom Responsive web layout to custom-oriented features, from WordPress to PHP, we can assist you in designing and developing a truly engaging experience for your customers on your chosen digital platform
https://www.seekace.com/
Really impressed! Everything is very open and very clear clarification of issues. It contains truly facts. Your website is very valuable. Thanks for sharing.
ReplyDeleteartificial intelligence course in bangalore
If you are unable to the Alexa Red Ring of death issue, then get in touch with our executives who are going to provide you with the best solutions. Call us on our toll-free number for instant solution USA/Canada: +1-844-607-7233 & UK: +44-800-041-8324. Get in touch with us.
ReplyDeleteGrat blog and very useful, thanks for sharing.
ReplyDeleteAre you fed up with the error Kindle won’t connect to wifi? Looking for the best solution? Then look no further than the ebook helpline. We are a team of dedicated and skilled technicians and we are available round the clock to help you. To know more visit our website.
ReplyDeleteThanks For Sharing The Information The Information Shared Is Very Valuable Please Keep Updating Us Time Just Went On Reading The article
ReplyDeleteBy Cognex is the AWS Training in chennai
I am a new user of this site so here i saw multiple articles and posts posted by this site,I curious more interest in some of them hope you will give more information on this topics in your next articles.
ReplyDeleteartificial intelligence course
I am a new user of this site, so here I saw several articles and posts published on this site, I am more interested in some of them, hope you will provide more information on these topics in your next articles.
ReplyDeleteArtificial Intelligence Course in Bangalore
You have completed certain reliable points there. I did some research on the subject and found that almost everyone will agree with your blog.
ReplyDeleteArtificial Intelligence Course in Bangalore
Great Post, Keep up the good work, thanks for sharing
ReplyDeletehire a freelancer in india
Happy New Year Wishes Shayari
ReplyDeleteShayari
They are produced by high level developers who will stand out for the creation of their polo dress. You will find Ron Lauren polo shirts in an exclusive range which includes private lessons for men and women.
ReplyDeleteData Science Course
ReplyDeleteExcellent Blog! I would like to thank for the efforts you have made in writing this post. I am hoping the same best work from you in the future as well. I wanted to thank you for this websites! Thanks for sharing. Great websites!
Data Scientist Course in pune
Beneficial information for user, OxyContin tablets 10 mg administered 12-hourly are equal to those achieved from oxycodone 5 mg administered 6-hourly. Oxycontin is a prescription medicine used to treat moderate to severe pain.
ReplyDeletebuy oxycontin 10mg
buy oxycontin 20mg
buy oxycontin 40mg
buy oxycontin 80mg
I have read your article, it is very informative and useful to me, I admire the valuable information you offer in your articles. Thanks for posting it ... PMP Certification in Hyderabad
ReplyDeletehttps://painmedsstore.blogspot.com/2020/11/what-you-know-about-adderall-and-what.html
ReplyDeletehttps://www.symbaloo.com/mix/buyroxicodoneonlineusa
https://www.symbaloo.com/mix/buyvicodinonlineusa
https://www.symbaloo.com/mix/buymethadoneonlineusa
https://www.symbaloo.com/mix/buymorphineonlineusa
https://www.symbaloo.com/mix/buytramadolonlineusa
https://www.symbaloo.com/mix/buyxanaxonlineusa1
https://www.symbaloo.com/mix/buyphentermine37-5mg
https://gumroad.com/buyhydrocodonecod https://buyadderallonline.000webhostapp.com/
ReplyDeletehttps://buyhydrocodoneonlineus.000webhostapp.com/ https://buyoxycodoneonline.000webhostapp.com/
https://buyroxicodoneonline.000webhostapp.com/
https://society6.com/buyhydrocodoneonline
https://gust.com/accelerators/buy-hydrocodone-online-1-405-621-3574
https://www.symbaloo.com/mix/buyadderallonlineusa2
ReplyDeletehttps://www.symbaloo.com/mix/buyhydrocodoneonlineus
https://www.symbaloo.com/mix/buydilaudid8mgonline
https://www.symbaloo.com/mix/buynorcoonlineinusa
https://www.symbaloo.com/mix/buypercocetonlineinus
https://www.symbaloo.com/mix/buyoxycodone15mg30mg
https://www.symbaloo.com/mix/buyoxycontin40mgonline https://customercare.webmd.com/hc/en-us/community/posts/360074039991-How-will-know-someone-has-an-addiction-to-buy-hydrocodone-online-or-not-in-usa-1-405-621-3574-
https://www.varindia.com/ask/question/where-can-you-buy-hydrocodone-overnight-shipping/
https://www.varindia.com/ask/question/how-will-know-someone-has-an-addiction-to-buy-hydrocodone-or-not/
https://www.plurk.com/buyhydrocodoneonline406
ReplyDeletehttps://mix.com/painmedsstore
https://www.pearltrees.com/georgemartin4563/buy-pain-medicine-online-usa/id34423472#l785
https://flipboard.com/@painmedsstore/buy-hydrocodone-order-hydrocodone-10mg-where-to-buy-hydrocodone-gd326lf1y
https://visual.ly/community/Infographics/health/how-buy-adderall-online-credit-card
This post is great. I really admire your post. Your post was awesome. data science course in Hyderabad
ReplyDeleteThank you so much for shearing this type of post.
ReplyDeleteThis is very much helpful for me. Keep up for this type of good post.
please visit us below
data science training
Thank you so much for shearing this type of post.
ReplyDeleteThis is very much helpful for me. Keep up for this type of good post.
please visit us below
data science training
Thank you so much for shearing this type of post.
ReplyDeleteThis is very much helpful for me. Keep up for this type of good post.
please visit us below
data science training
ReplyDeleteTook me time to understand all of the comments, but I seriously enjoyed the write-up. It proved being really helpful to me and Im positive to all of the commenters right here! Its constantly nice when you can not only be informed, but also entertained! I am certain you had enjoyable writing this write-up.
artificial intelligence course in bangalore
This is an awesome motivating article.I am practically satisfied with your great work.You put truly extremely supportive data. Keep it up. Continue blogging. Hoping to perusing your next post
ReplyDeleteDigital Marketing Training Institutes in Hyderabad
DR SALATO HERBAL MEDICINE FOR PENIS ENLARGEMENT drsalatosolutiontemple@gmail.com or visit His website http://drsalatosolutionte0.wixsite.com/drsalato , you can call/whatsapp him via +2348103629945 hello everyone here i am medical doctor from UK but currently in NEW YORK i want to share a great testimony of how Dr SALATO herbal mixture cream saves me from shame and disgrace, my penis was a big problem to me as the size was really so embarrassing and discouraging, a 35 year old grown man like me having 3.5 inches penis and to worsen it i don't last more than 10 minute in bed it was really a thing of shame my wife was really tired of me because my sex life was very very poor , she never enjoyed sex with me, i was always thinking and searching for a solutions everywhere until last one months ago when i saw a testimony of how Dr SALATO herbal mixture cream have been helping people around the globe,i saw one MR TIMOTHY testifying of how Dr SALATO helped him enlarge his penis size from 4 to 8 inches so i decided to give him a try ,i visited his website link https://drsalatosolutionte0.wixsite.com/drsalato we talked and he gave me steps to follow which i did and to my greatest surprise in less than two weeks of taking the herbal mixture cream my penis grow to 7 inches i couldn't believe my eyes and as i speak now my penis is now 9 inches long and i was amazed when my wife said i satisfy her so well in bed now all thanks to Dr SALATO herbal mixture cream,i will forever be grateful To him i also learnt that Dr SALATO also have the herbal cure to problems likePENIS ENLARGEMENTERECTILE DYSFUNCTIONDIABETES type 1 and type 2HERPES GENITAL WARTLOW SPERM COUNTWEAK ERECTIONBREAST ENLARGEMENTPROSTATE CANCERHIV/AIDSSPELL OF ALL KINDS LIKE EX BACK,CANCEL DIVORCE,BREAK UP SPELL ,PREGNANCY SPELL,PROMOTION SPELL,JOB SPELLALSHPV 123PILEASTHMAHEART FAILUREPREMATURE EJACULATIONHEPATITIS A,B,C AND MANY MOREso if you are suffering from any of these problems please do not hesitate to contact him now email drsalatosolutiontemple@gmail.com or visit His website https://drsalatosolutionte0.wixsite.com/drsalato , you can call/whatsapp him via +2348103629945 THANKS
ReplyDeleteNice & Informative Blog !
ReplyDeleteIf you are looking for the best accounting software that can help you manage your business operations. call us at QuickBooks Customer Service Number 1-855-974-6537.
Hey! Amazing work. With full of knowledge. Our Team resolve any glitches occurring while utilizing the software. Looking Quickbooks Error 1723 1-855-756-1077. Our experts will assist you to fulfil your accounting needs. The solutions are accurate and time-saving.
ReplyDeleteNice & Informative Blog !
ReplyDeleteQuickBooks is a feature-rich accounting software that has contributed to the growth and development of businesses.To fix such problems, do call us at QuickBooks Customer Service Number 1-855-974-6537 for instant help.
ReplyDeleteI see some amazingly important and kept up to length of your strength searching for in your on the site
Best Institute for Data Science in Hyderabad
I like this post and there is obviously a lot to know about this. I think you made some good points in Features also i figure that they having a great time to peruse this post. They might take a decent site to make an information, thanks for sharing it to me Keep working, great job!
ReplyDeleteBraces in Bangalore
Aivivu, chuyên vé máy bay, tham khảo:
ReplyDeleteVe may bay di My
vé máy bay từ mỹ về việt nam 2021
mua vé máy bay từ đức về việt nam
vé máy bay giá rẻ từ nga về việt nam
Nice and very informative blog, glad to learn something through you.
ReplyDeletedata science course malaysia
What a really awesome post this is. Truly, one of the best posts I've ever witnessed to see in my whole life. Wow, just keep it up.
ReplyDeletedata science online course
Just saying thanks will not just be sufficient, for the fantasti c lucidity in your writing. I will instantly grab your rss feed to stay informed of any updates.
ReplyDeleteData Science Course in Mangalore
Hi, I looked at most of your posts. This article is probably where I got the most useful information for my research. Thanks for posting, we can find out more about this. Do you know of any other websites on this topic?
ReplyDeleteData Science Course in Jaipur
I don t have the time at the moment to fully read your site but I have bookmarked it and also add your RSS feeds. I will be back in a day or two. thanks for a great site.
ReplyDeleteData Science Course in Mysuru
Infertility specialist in chennai
ReplyDeleteSexologist in chennai
Sexologist doctor in chennai
I am a new user of this site so here i saw multiple articles and posts posted by this site,I curious more interest in some of them hope you will give more information on this topics in your next articles.
ReplyDeleteData Science Course in Trichy
With so many books and articles coming up to give gateway to make-money-online field and confusing reader even more on the actual way of earning money,
ReplyDeleteData Science Course in Trichy
I will be honest these is the most useful tips I have read till date. Thanks for putting all this together. As a newbie blogger, I am going through different stages of learning and all ups and downs what a normal newbie blogger face. But the most important thing I am not giving up and holding it until I find success. I am really positive using your thoughts and knowledge will help me to improve myself. Siberian husky Puppies for adoption Great work. Keep doing this great work for us. Loved it.
ReplyDeleteNice Blog !
ReplyDeleteAre you looking for extensive solutions for QuickBooks Error 12152? Do not worry at all. Just reach us via our QuickBooks Error Support Number and solve all your troubles related to QuickBooks in less time.
I want to say thanks to you. I have bookmark your site for future updates.
ReplyDeletebusiness analytics course
Thanks for sharing good information.
ReplyDeleteCloud computing
I'm an account manager willing to help those that have lost their money to scammer in one way or another trading. I give you my word that i will meet up with the following criteria
ReplyDelete$1000 get $14,000
$1,500 get $19,000
$2,500 get $25,000
$4,500 get $30,000 – You can create your own account with our recommended broker, then you have access to it at anytime, and send me the detail for management – 80% guaranty profit, With a minimum investment of $250 ? Payout within {24} hours after the end of every trading period.
Success is for risk takers? i take the risk back then now i can prove to you that success is my other name if interested email me via KRESTINVEST@PROTONMAIL.COM
Are you searching for different types of drugs like ADHD, Ritalin, Phenida, etc in the USA and another country? So Buy without prescription medicine here. We are the best pharmacy in the USA. We provide all types of drugs with an overnight shipping facility.
ReplyDeletewww.office.com/setup– To Install Office setup Enter office setup product key and activate, setup office, visit Microsoft office at www.office.com/setup and Get Installed.
ReplyDeletenorton.com/setup - For Downloading, Installing and activating the Norton product, visit www.norton.com/setup and Get Started with Norton Antivirus at www.norton.com/setup .
mcafee.com/activate
Kashmir tour packages
Keep it up your good work, I read your's website, I think that your blog is fascinating and has sets of the fantastic piece of information. Thanks for your valuable efforts
ReplyDeleteIf you face QuickBooks Error 404, please visit:
quickbooks error 4
Attend The Data Science Courses Bangalore From ExcelR. Practical Data Science Courses Bangalore Sessions With Assured Placement Support From Experienced Faculty. ExcelR Offers The Data Science Courses Bangalore. chiffon suits wholesale , chiffon suits wholesale
ReplyDeleteExcellent Blog! I would like to thank for the efforts you have made in writing this post. I am hoping the same best work from you in the future as well. I wanted to thank you for this websites! Thanks for sharing.
ReplyDeleteHLA
Nice Blog !
ReplyDeleteOur team at QuickBooks Customer Service work continuously 24/7 around the clock during disastrous times.
https://www.buyfentanylc.com/product/buy-ritalin-online/
ReplyDeletehttps://www.buyfentanylc.com/product/buy-vyvanse-10mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-20mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-30mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-40mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-50mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-60mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-70mg-online/
https://www.buyfentanylc.com/product/buy-vyvanse-online/
learn Digital marketing
ReplyDeleteI just got to this amazing site not long ago. I was actually captured with the piece of resources you have got here. Big thumbs up for making such wonderful blog page!
ReplyDelete<a href="https://360digitmg.com/india/artificial-intelligence-ai-and-deep-learning-in-pune
>artificial intelligence course in pune</a>
Highly appreciable regarding the uniqueness of the content. This perhaps makes the readers feels excited to get stick to the subject. Certainly, the learners would thank the blogger to come up with the innovative content which keeps the readers to be up to date to stand by the competition. Once again nice blog keep it up and keep sharing the content as always.
ReplyDeleteData Science certification in Bhilai
ReplyDeleteI truly like your composing style, incredible data, thank you for posting.
Best Institute for Data Science in Hyderabad
ReplyDeleteSuperb. I really enjoyed this article here. Really it is an amazing article I had ever read. I hope it will help a lot for all. Thank you so much for these amazing posts and please keep updating this excellent article.Thank you for sharing such a great blog with us. expecting for your.
Digital marketing in Jaipur
Thanks for sharing this great article! That is very interesting I loved reading and I am always searching for informative information like this.
ReplyDeleteData Science Course in Vadodara
Really awesome blog. Your blog is really useful for me. Thanks for sharing this informative blog. Keep update your blog.
ReplyDeleteMasters in Data Science Pune
Get 10% off on use coupon- "SALE10"
ReplyDeleteAll type of medicines available online 24*7 in Xanax stores and fast home delivery so get it now.
Order here-
Buy Ambien Online
Buy Dilaudid Online
Buy Ativan Online
Buy Adderall Online
Buy Tramadol Online
Buy Methadone Online
Buy norco online
Buy Percocet Online
Buy Xanax Online
Ambien 10mg is an online medical store and online pharmacy that provides its customers with the best experience in buying medicines online.
ReplyDeleteVisit Website: Best Online Pharmacy in US
Order Adderall from here at 25% OFF - Buy Adderall Online
Order Ambien from here at 25% OFF - Buy Ambien Online
Order Xanax from here at 25% OFF - Buy xanax Online
Order Tramadol from here at 25% OFF - Buy Tramadol Online
3. Love to read this amazing and helpful post.
ReplyDeleteI specially congratulate you for this kind of post.
Satta Matka Game App Development
Satta Matka Game App Development
https://www.gowebs.in/satta-matka-software-development
Obviously, your post extremely good After reading this post. Keep it up
ReplyDeleteTop 50 Web Designers in Baripada Bazar, Mayurbhanj
Website Design in Baripada (M), Mayurbhanj, Orissa - Rs999,
Web Design Service in Baripada,
Best Logo Design Company in Baripada,
Website Design Cost in Baripada,
Top 50 Web Designers in Baripada Bazar, Mayurbhanj
website design baripada
website design baripada
https://www.gowebs.in/web-design-Baripada
Thanks for such a wonderful content. Our Motive is not just to create links but to get them indexed as will
ReplyDeleteIncrease Domain Authority (DA).We’re on a mission to increase DA PA of your domain
High Quality Backlink Building Service
Boost DA upto 15+ at cheapest
Boost DA upto 25+ at cheapest . Very Helpful
Buy xanax online
ReplyDeleteXanax belongs to the benzodiazepines drug, which is using to address anxiety, panic disorder, and stress by stimulating the disturbed and unbalanced chemicals in the brain. Xanax offers calming effects in the brain to enhance the productivity level. Butor’s consultation and guidelines. Buy Xanax online
Buy xanax online
ReplyDeleteXanax belongs to the benzodiazepines drug, which is using to address anxiety, panic disorder, and stress by stimulating the disturbed and unbalanced chemicals in the brain. Xanax offers calming effects in the brain to enhance the productivity level. Butor’s consultation and guidelines. Buy Xanax online
Buy hydrocodone online
ReplyDeleteThis combination medication is used to alleviate moderate to severe pain. Hydrocodone contains both the things an opioid (narcotic) pain reliever (hydrocodone) and a non-opioid pain reliever (acetaminophen). Hydrocodone works inside the brain to vary how your body adjusts feels and responds to pain. buy hydrocodone online
Buy adderall online
ReplyDeleteAdderall Online is being used under the observation of health experts to address ADHD and narcolepsy without causing any future health issues. Therefore, It works to promote a healthy and progressive mindset by reducing the impact of aggression, stress, and anger. and the formula of Adderall is C9H13N.buy adderall online
Buy oxycontin online
ReplyDeleteOxycontin may be a brand of Oxycodone, this is often the controlled-release Oxycodone tablets, intended to be taken every 12 hours.Oxycodone may be a semi-synthetic opioid synthesized from thebaine, an opioid alkaloid found in the Persian poppy, and one among the various alkaloids found within the Papaver somniferum. buy oxycontin online
Buy norco online
ReplyDeleteNorco may be a powerful prescription pain drug that comprises an opioid (narcotic) that’s utilized to regulate pain severe sufficient to wish an opioid analgesic , while other pain therapies like non-opioid ache medicines don’t manage your illness well adequately, otherwise you cannot bear them. Buy norco online
Buy vicodin online
ReplyDeleteThis drug helps in relieving moderate to severe pain. Vicodin contains a narcotic analgesic (hydrocodone) and a non-opioid pain reliever (acetaminophen). Hydrocodone helps the brain to change how your body feels and responds to pain.buy vicodin online
Nice Blog, i really want to read more about this topic, please keep posted regularly.
ReplyDeleteIf you face any Error or Error 404 in QuickBooks then immediately contactQuickbooks Error 404for best solution.
Hi there,
ReplyDeleteThank you so much for the post you do and also I like your post, Are you looking for Alprazolam Buy Online in the whole USA? We are providing Buy Vyvanse 30mg Capsules Online, Buy Ativan 2mg pills online, Buy Diazepam 10mg Pills online, Buy Oxycodone 80mg Pills online, ALPHABOL , Adderall Buy Online, Buy ketamine drug the well price and our services are very fast.
Click here for
Contact +1(205)392-8609
Thank you for sharing this valuable content.
ReplyDeleteI love your content it's very unique.
DigiDaddy World
Very great post. I simply stumbled upon your blog and wished to mention that I have really loved browsing your weblog posts. After all I will be subscribing to your feed and I'm hoping you write again very soon! national archives civil war
ReplyDeleteIt was reaaly wonderful reading your article. # BOOST Your GOOGLE RANKING.It’s Your Time To Be On #1st Page
ReplyDeleteOur Motive is not just to create links but to get them indexed as will
Increase Domain Authority (DA).We’re on a mission to increase DA PA of your domain
High Quality Backlink Building Service
1000 Backlink at cheapest
50 High Quality Backlinks for just 50 INR
2000 Backlink at cheapest
5000 Backlink at cheapest
Really it is very nice one Post. Thanks a lot for writing this post. Here I am posting about how to Career in Digital Marketing. Rision Digital is a site that helps you to Learn Digital Marketing & Blogging.
ReplyDeleteSuch as useful information. I really like this blog posting site. Thanks for sharing it.
ReplyDeleteSMS Non Woven Fabric Manufacturer | Non Woven Fabric Supplier
Such as useful information. I really like this blog posting site. Thanks for sharing it.
ReplyDeleteSMS Non Woven Fabric Manufacturer | Non Woven Fabric Supplier
ReplyDeleteVERY HELPFULL POST
THANKS FOR POSTING
MERN STACK TRAININIG IN DELHI SASVBA
ARTIFICIAL INTELLIGENCE INSTITUTE IN DELHI SASVBA
MACHINE LEARNING TRAINING IN DELHI SASVBA
DEEP LEARNING TRAINING IN DELHI NCR SASVBA
GMB
SASVBA
FOR MORE INFO:
Helpful information shared by this post. StaffMerge is the Employer Platform and job board for both employers and job seekers to make hiring and job search easier.
ReplyDeleteWow! Such an amazing and helpful post this is. I really really love it. It's so good and so awesome. I am just amazed. I hope that you continue to do your work like this in the future also
ReplyDeletedigital marketing courses in hyderabad with placement
This is my first time visiting. This is the place to be. I'm very excited to see this blog, and I appreciate you sharing this extremely useful material.
ReplyDeleteAffiliate Marketing Training In Telugu
I feel very grateful that I read this. It is very helpful and very informative and I really learned a lot from it.
ReplyDeleteBest Data Science courses in Hyderabad
Npower recruitment portal is open. All you need to do is Npower login and the official portal is npower application website for the recruitment of new npower applicants.
ReplyDeleteThis knowledge.Excellently written article, if only all bloggers offered the same level of content as you, the internet would be a much better place. Please keep it up.
ReplyDeletedata scientist training in hyderabad
This post is very simple to read and appreciate without leaving any details out. Great work!
ReplyDeletebusiness analytics course
Thanks for sharing such informative content. Our writers are well equipped to handle different types of academic papers and it therefore goes without saying that once you order for our Capstone writing services your entire academic writing challenges shall be no more.
ReplyDeleteThanks a lot for sharing kind of information. Your article provides such great information with good knowledge. Digital Marketing Courses in Pune with Placement
ReplyDeleteYou have now arrived and are locked-in to a perpetual cycle. salesforce training in noida
ReplyDeleteHi, I looked at most of your posts. This article is probably where I got the most useful information for my research. Thanks for posting, we can find out more about this. Do you know of any other websites on this topic
ReplyDeleteData Science Course in Delhi
ReplyDeleteacheter adderall 30mg
acheter ambien
acheter ativan 2mg
acheter de lheroine
acheter de lhydrocodone
acheter de loxycodone
acheter demerol en ligne
acheter dilaudid hp injection
acheter du ritalin
We are very thankful for share this informative post. We have an online store for Motogp Leather Suits & Jackets buy with worldwide free shipping.
ReplyDeleteMotogp Leather Suits
Motogp Leather Jacket
Call girls in Rawalpindi
ReplyDeleteEscorts in Murree
Escorts Service Murree
I think about it is most required for making more on this get engaged.
ReplyDeletebusiness analytics course
Your efforts are much appreciated. Nobody will be able to look at you without admiring you. Many thanks for sharing.
ReplyDeletedigital marketing training in hyderabad
digital marketing course in ameerpet
digital marketing course training in hyderabad ameerpet
Thanks for sharing nice information....
ReplyDeletedata science course in pune
We have the best escorts service in #Murree for book your escort call now 03013777277
ReplyDeleteSex in Islamabad
Sexy Escorts in Islamabad
Prostitute in Islamabad
Informative article. Thanks for sharing with us.keep it up.
ReplyDeletemachine learning courses in aurangabad
This was really one of my favorite website. Please keep on posting.
ReplyDeletedigital marketing courses in hyderabad with placement
ReplyDeleteNice post. I used to be checking constantly this blog and I am impressed! Extremely useful info particularly the ultimate section 🙂 I take care of such information a lot. I was seeking this certain information for a long time. Thank you and best of luck.
Report writing on blood donation camp
Great post I must say and thanks for the information. Education is definitely a sticky subject. However, is still among the leading topics of our time. I appreciate your post and look forward to more. google ads promo code
ReplyDeleteVery informative post
ReplyDelete